Posted by Virus Bulletin on Jun 21, 2012
New tool aims to enhance conference networking opportunities.
For many in the security industry, the Virus Bulletin conference is the highlight of their busy events calendar, and one of the most valuable aspects of the event is the opportunity to network with other industry members.
Since the inaugural event in 1991, the VB conference has enabled experts from around the globe to share their ideas and discoveries with colleagues. Virus Bulletin believes cooperation is essential in the fight against malware and spam, and the VB conference plays an important part in facilitating such cooperation.
But cooperation doesn't stop after the closing slides of the conference. Neither does it automatically happen when people are at the same event: with new delegates and new companies being represented every year, it isn't always clear who is who, who does what, or even which part of the hotel bar people are holed up in!
To help enhance delegates' networking opportunities at the conference, Virus Bulletin has built VBConnect - a (closed) social network for VB conference delegates. It allows delegates to present themselves on a profile page and to find others based on keywords such as their research interests. It also allows delegates to send each other messages - for instance to arrange meetings at the conference. It will also continue to work after the conference has ended.
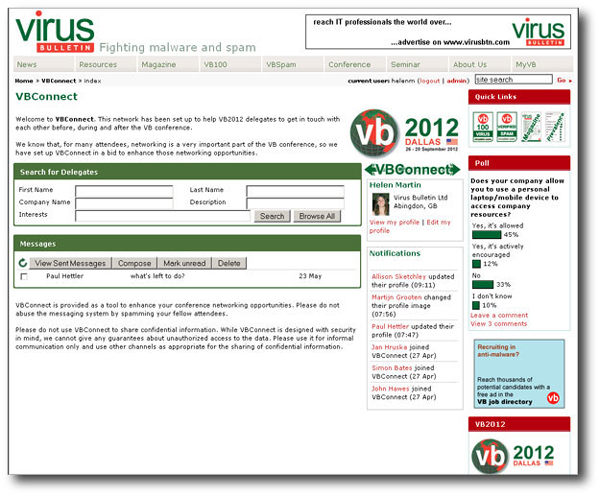
VBConnect is already available for registered VB2012 delegates. If you haven't registered yet, why not register now? VB2012 takes place 26-28 September 2012 at the Fairmont Dallas hotel, Dallas, TX, USA. You can see the conference programme here.
Posted on 26 June 2012 by Virus Bulletin