Posted by Virus Bulletin on Mar 18, 2013
Meanwhile, desktop users sent to (relatively harmless) weight-loss site.
Links found in certain spam emails which redirect desktop users to a phony weight-loss website, have been found to send mobile users to a trojan proxy, according to researchers at Lookout.
Clicking links in spam emails falls into the "don't try this at home" category, but if you do so in a safe environment, as I have done, you will notice that quite a lot of spam (particularly spam sent from compromised webmail accounts) links to sites advertising weight-loss products and vaguely resembling Fox News.

Given the amount of spam that links to exploit kits such as 'Blackhole', linking to a weight-loss site seems relatively harmless. However, things may be rather different if you click the link on a mobile device.
Researchers at mobile security firm Lookout have discovered that the final destination of these links depends on the type of browser used: while desktop browsers redirect to the weight-loss site, mobile browsers are sent to a download of the 'NotCompatible' trojan. When installed, this turns the device into a proxy. When it was first discovered last year, the proxy was used by crooks to buy concert tickets and to make purchases in the Apple Store, probably using stolen credit cards.
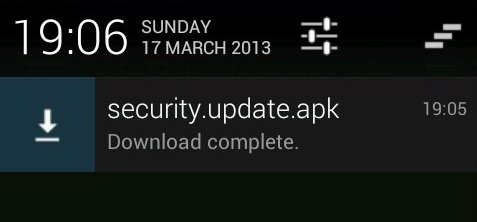
We have been able to confirm Lookout's claims. Somewhat worryingly, on the device we tested, we were not prompted about the download, but merely received a notification confirming that a 'Security Update' had been downloaded. As users have become more security-aware, even on mobile devices, many may ignore this alert, believing it to be something positive.
More at Lookout's blog here.
Posted on 18 March 2013 by Martijn Grooten