Posted by Virus Bulletin on May 31, 2013
Eased restrictions welcomed by security experts.
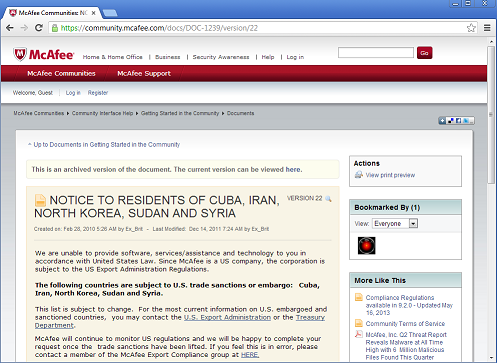
The United States has announced it has eased export restrictions to Iran, and now allows for the export of mobile phones and software, including anti-virus software.
The US originally imposed sanctions against Iran following the Iranian Revolution of 1979 and has tightened them several times since, among other things because of the country's alleged nuclear program. While the effect of economic sanctions is debated among experts, the fact that anti-virus software could not be exported has regularly received criticism from security and privacy experts.
The Iranian government is known to have regularly intercepted its citizens' online communications (for example by using SSL certificates generated by hacking into the DigiNotar certificate authority) and it is well possible that spyware is also used. However, it wouldn't be the only government to do so: this week, the US entertainment industry released a report in which it argued for the use of ransomware against piracy. But at least US citizens would be able to purchase security software that would, hopefully, allow the detection of such programs.
If citizens in a foreign country are not allowed to purchase security software, they would be forced either to do without such software, or to use whatever their own government provides them with; hardly a reassuring thought. A similar argument can be made about the use of communication technology, such as mobile phones; hence the ban on the export of these has also been lifted.
There is one notable exception to the eased restrictions: software and mobile phones cannot be sold if the seller has reason to believe they are going to be used by the Iranian government. The Iranian government will thus have to find its own solutions against new Stuxnet variants.
More at the BBC here with a PDF of the updated regulations by the Office of Foreign Assets Control here.
Posted on 31 May 2013 by Martijn Grooten