Posted by Virus Bulletin on Jul 11, 2013
Little-used feature could have unintended security consequences.
As the Internet is (very) slowly migrating towards IPv6, researchers are reconsidering a little-used feature that allows for IPv6 packets to be fragmented by the sender and reassembled by the recipient.
Last year, we published an article on the security implications of the transition from IPv4 to IPv6. Some of these implications are a direct consequence of the incredibly large space of IP addresses: IP-based reputation services, such as DNS blacklists, will become a lot harder to maintain, while the fact that IPv6 does away with NAT makes any IPv6-connected device publicly routable - which will be greatly appreciated by those running botnets.
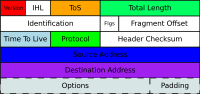
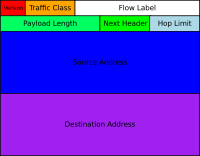
But IPv6 isn't merely IPv4 with a larger address space. It's a new protocol, where some of IPv4's properties have been removed (most notably the checksum, which is computed in a different layer), while new features have been added to allow for more flexibility. While this is a good thing, it also means that new software packages had to be written to deal with IPv6 packets - which are guaranteed to have vulnerabilities. It may also be that some of these new features have unintended consequences.
I was reminded of this when I read a blog post by Arbor Networks' Bill Cerveny, who pointed to an IETF draft that proposes deprecating IPv6 fragment headers.
One feature of IPv6 is the ability of packets to be split up into fragments at the source and then reassembled at the destination. This allows for the sending of large packets, even if one of the links connecting destination and source happens to have a low Maximum Transmission Unit (MTU).
In practice, however, fragmentation and defragmentation of packets is resource intensive, and applications are encouraged instead to determine the path MTU: the smallest MTA of one of the links, or, as equivalent, the largest packet size that can be sent over the connection.
But it isn't merely inefficiency that is the problem with packet fragmentation: the IETF draft explains how fragmented packets can be used to bypass stateless firewalls that inspect each packet separately. Researchers have also found a number of ways in which cleverly crafted fragmentation packets can have unintended consequences and can, for instance, perform a DDoS attack on the recipient.
IETF discussions tend to take a long time and, as Cerveny points out, there are some cases where there may be no good alternatives to the use of IP fragments; hence it is far from clear whether packet fragmentation will end up being deprecated. And even if it is, we will have to wait and see if software will indeed stop allowing for IPv6 packets to be sent or received in fragments.
But it does point to a general issue with IPv6: as a new protocol, it is well possible that some of its lesser-known features, or their implementations in software, contain vulnerabilities. While it is good that security researchers are working hard to find such vulnerabilities, there will always be some that won't appear until they are being used in the wild.
For that reason, the rather slow adoption of IPv6 may actually be a blessing. True, it would be a disaster for the Internet if the migration were to stop - as we really will end up running out of IPv4 addresses. But to rush the migration to a new and relatively untested protocol would be even worse.
Posted on 11 July 2013 by Martijn Grooten