Posted by Virus Bulletin on Sep 5, 2013
New Tor version should help the network deal with increased traffic.
Sometimes a picture says more than a thousand words:
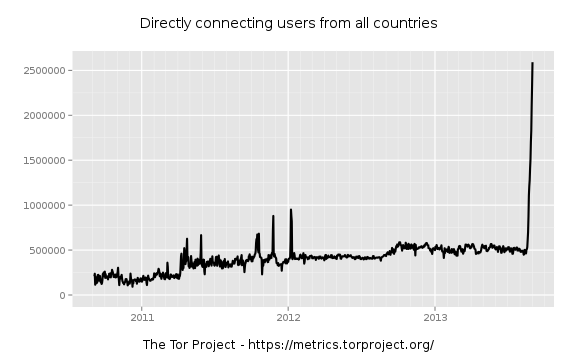
The graph shows the daily number of users of the Tor anonymity network over the past three years. As both the network and concerns over anonymity have grown, the usage has shown a slow but steady growth, with the occasional short peak. And then suddenly, in the third week of August this year, the number of users started to grow very quickly, resulting in a five-fold increase in barely two weeks.
Such a sharp increase cannot simply be explained by increased fears over surveillance, especially given that there was no noticeable increase in Tor usage directly following Edward Snowden's PRISM revelations.
Some have suggested that the release of PirateBrowser, a web browser designed to circumvent censorship that uses Tor, was the reason for the huge increase, but this seems unlikely: the browser was released well before the number of Tor users started to grow, and it uses the FoxyProxy Firefox plug-in - the use of which didn't see such a huge increase.
A more likely explanation would be that a botnet is responsible for the increased use of Tor.
Botnets using Tor for command and control communications aren't new. Neither are botnets that use Tor to hide the location of their nodes when performing a malicious activity: leaving comment spam on websites appears to be commonly done through Tor.
Researchers have been searching for evidence of such a botnet. Today, Fox-IT's Yonathan Klijnsma writes about a botnet that could well explain the surge in Tor users.
The malware he analysed isn't new and is known as 'Mevade' or 'Sefnit', while to those running it may be known as 'SBC'. Recently, coinciding with the increase in Tor users, it switched to Tor for its C&C communication. Both the size of the botnet and the particular Tor version used add to the belief that this is indeed what has caused the increase.
It is less clear what the purpose of the botnet is. Klijnsma suggests that the botnet - which he believes to originate in the former Soviet Union - may be used to load additional malware onto the system and that it (or parts of it) is offered for sale. He believes the ultimate motive is financial gain.
The latter may be a relief for many of Tor's supporters, who worried that this was a DDoS attack against the service itself, possibly by an entity that doesn't like the idea of people using online anonymity. The fact that, rather uniquely, there has been no increase in Tor users in Israel had already provided fuel for conspiracy theories.
While a botnet consisting of millions of users is clearly harmful for the Internet as a whole, it is particularly harmful for Tor, whose four thousands nodes could barely deal with the increased traffic. In a blog post for the project, Tor's Roger Dingledine explains how some improvements to the protocol have been made that should help the network deal better with the increase in traffic.
The natural next step after the discovery of a large botnet would be to attempt to take it down. Normally this would involve shutting down, or taking over, the botnet's command and control servers, but given their hidden nature, this will not be an easy task.
The anonymous nature of Tor also means that we will never be certain whether this particular botnet is responsible for the sharp increase in users. But assuming it is, I worry this isn't the last we have heard of it. Hopefully security researchers will find a way to shut down the botnet and thus help the Internet in general, and Tor in particular.
Posted on 5 September 2013 by Martijn Grooten