Posted by Virus Bulletin on Jan 29, 2014
Credentials sent to attacker by built-in SMS functionality.
Modems and routers aren't typically known for their security, and modems that allow one to connect to mobile broadband are no exception. Now, a Swedish security researcher has discovered how this lack of security can be exploited in a spear-phishing attack that requires only very minimal infrastructure.
Andreas Lindh, whom readers may remember from his VB2013 presentation, looked into a 3G/4G USB modem: a device that can be plugged into a laptop's USB port and then connect to the Internet via a built-in SIM card.
Lindh found the modem's web interface vulnerable to a cross-site request forgery (CSRF) attack. In fact, one could argue that this vulnerability was there by design: the web interface did not require any kind of authentication, which means that tricking the user into visiting a specially crafted website would suffice to have tasks on the interface executed.
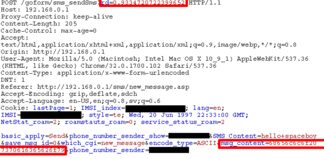
Most of these tasks, such as enabling or disabling roaming, or adding a profile, would be nothing but a mild nuisance and thus of little interest to an attacker. But by figuring out what parameters were used in the relevant HTTP POST request, Lindh found he was also able to make the device send text messages.
It's not hard to see how an attacker could turn this hack into a money-making scheme by having the modem send SMS messages to a premium rate number under their control. But it can also be used in a rather cunning spear-phishing attack, which would be especially useful given that these modems are mostly used by corporate customers.
To show how this would work, Lindh created a fake Facebook login page using the data URI scheme, which means that the whole page is contained inside the URI. He then used a URL shortener to turn this page into a short link that could be sent over email.
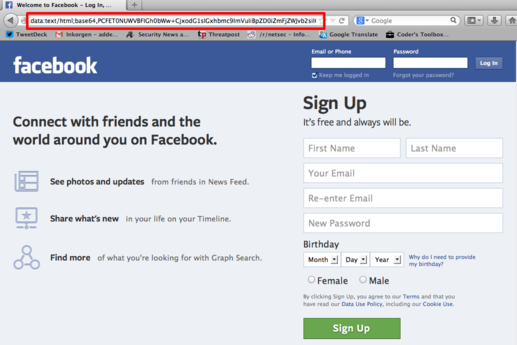
The page was made so that upon entering valid credentials, the user would be logged into the real Facebook - but in the background, the credentials would be sent to the attacker by text message.
What is neat from an attacker's point of view - and thus worrying from a security point of view - is that the attack requires barely any infrastructure. In particular, it doesn't require the attacker to host a website and a command and control structure. All an attacker needs are an email address and a mobile phone number.
Are you using your hacking skills to make the Internet safer? Why not submit an abstract for VB2014, which will take place 24-26 September 2014 in Seattle, WA, USA. 'Hacking & vulnerabilities' is the subject of one of the six themed sessions for this conference. The deadline for submissions is 7 March 2014.
Posted on 29 January 2014 by Martijn Grooten