Posted by Virus Bulletin on Apr 7, 2014
Security firm advises regenerating keys and replacing certificates on vulnerable servers.
A very serious vulnerability in OpenSSL has caused panic among network administrators: CVE-2014-0160 allows an attacker to read the memory of a vulnerable server and thus obtain private encryption keys, passwords and other kinds of sensitive information.
OpenSSL is a widely used open-source implementation of the SSL and TLS cryptography protocols. It is used by many web servers and other online services to prevent adversaries from eavesdropping on sensitive information. The vulnerability was introduced in OpenSSL 1.0.1, which was released in March 2012. It was fixed in OpenSSL 1.0.1g, released yesterday.
The vulnerability has been named 'Heartbleed', after the heartbeat extension that adds session management to TLS connections, in the implementation of which the vulnerability resides.
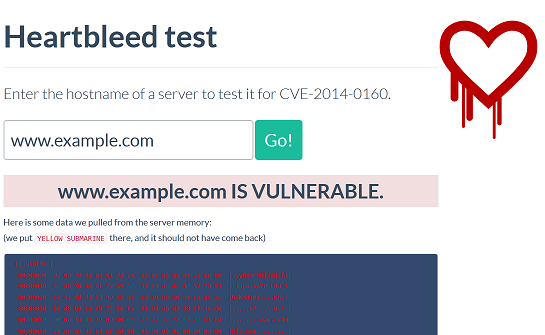
An attacker can connect to a vulnerable server and use the vulnerability to read up to 64 kilobytes of the server's memory. While the attacker has no control of which memory segment it obtains, there is no limit to the number of times the attack can be performed; hence it can effectively be used to perform a remote memory dump. To make matters worse, the way the heartbeat protocol is implemented means that attack activity is not logged.
Luckily, the attack can be detected on the network, albeit not retroactively. Security firm Fox-IT has released a number of Snort signatures that detect successful exploitation of the vulnerability.
The vulnerability was discovered independently by researchers from Google and Finnish security firm Codenomicon. The latter set up a useful website with a number of frequently asked questions about the vulnerability. There is no reason to assume that the vulnerability hasn't also been discovered by an entity that doesn't have the best interests of the Internet at heart.
Unlike the recent 'goto fail' vulnerability in OS X (and a similar one in GnuTLS), the vulnerability doesn't require a man-in-the-middle attack to be performed. Once an attacker has used the vulnerability to obtain the server's private signing keys, these can of course be used to perform man-in-the-middle attacks.
Fixing the vulnerability is easy - simply upgrade to OpenSSL 1.0.1g. But that doesn't stop attackers who have previously obtained the private keys. Hence it is important to follow the advice given by Fox-IT - to regenerate the private keys and replace the SSL certificates - even if it is a rather painful and possibly expensive procedure.
A website has been set up to check if your server is vulnerable, though that reportedly can give false positives. In the meantime, given the huge impact of this vulnerability, one is right to wonder if OpenSSL shouldn't be considered critical infrastructure.
Posted on 08 April 2014 by Martijn Grooten