Posted by Virus Bulletin on Jul 10, 2014
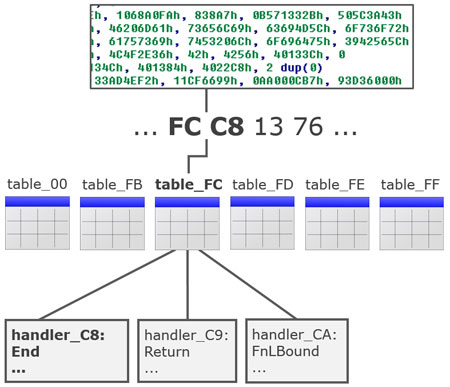
Marion Marschalek looks at two Miuref binaries: one packed with Visual Basic 6 and one with C++.
Two months ago, Microsoft announced it had added 'Miuref' to its Malicious Software Removal Tool. First discovered in December 2013, Miuref is a click-fraud trojan that silently makes a browser 'click' advertisements that are controlled by those running the malware.
As cybercrime goes, click-fraud is a relatively low-level kind of crime. That doesn't mean it's something we shouldn't worry about though. Nor does it mean that those running the malware don't go to great lengths to prevent their malicious applications from being detected or analysed.
Today, we publish a paper by Marion Marschalek, a researcher at Cyphort, in which she analyses two Miuref binaries that were spread via the Fiesta exploit kit through the website of a popular men's lifestyle magazine. One binary was packed using a Visual Basic 6 packer, while the other one was compiled using C++. In the paper, Marion not only takes apart both samples, she also shares her excitement and frustration in doing so, making it an interesting read for anyone involved in malware analysis.
Remember that, as of this month, all papers published through Virus Bulletin are available free of charge. You can download this paper here in HTML format, or here as a PDF (no registration required).
Posted on 10 July 2014 by Martijn Grooten