Posted by Virus Bulletin on Aug 7, 2014
Despite short spike, image spam no problem for spam filters.
Good news for those who need to run a spam filter (in other words: everyone who runs a mail server). For the second time in a row, all 15 participating full solutions in our comparative anti-spam tests achieved a VBSpam award. They all blocked a large percentage of spam, while blocking very few legitimate emails.
Eight products – Bitdefender, ESET, FortiMail, Kaspersky LMS, Libra Esva, Netmail Secure, OnlyMyEmail and ZEROSPAM – even achieved a VBSpam+ award for blocking more than 99.5% of spam, while generating no false positives at all in the 'ham' corpus, and very few false positives in a separate corpus of newsletters.
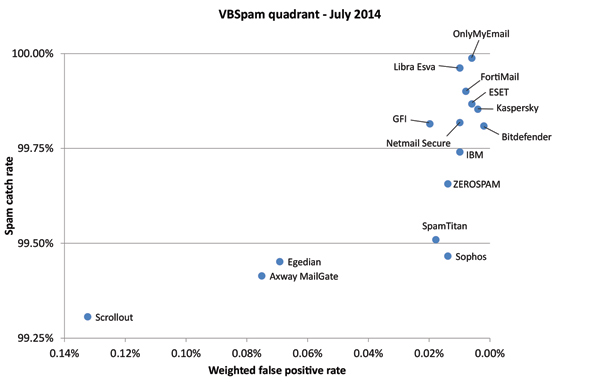
This month's results didn't only provide good news. The relative amount of spam missed increased by a third and while with an average catch rate of 99.7% there isn't a lot to worry about yet, this is something for product developers to keep an eye on. In the spammers' business model, a high block rate is already included, so a small change can make or break a spam campaign.
As of this month, all content published through Virus Bulletin is available free of charge, and the test reviews are no exception. We encourage readers to make use of this and read the report, if not for the performance details of the various products, then at least for the 'state of spam' overview these bi-monthly reports provide.
This month's report has been split in two. A summary of the results with a focus on the state of spam can be viewed here in HTML format, or downloaded here as a PDF. The full report, with performance details of all participating products, can be viewed here in HTML format, or downloaded here as a PDF.
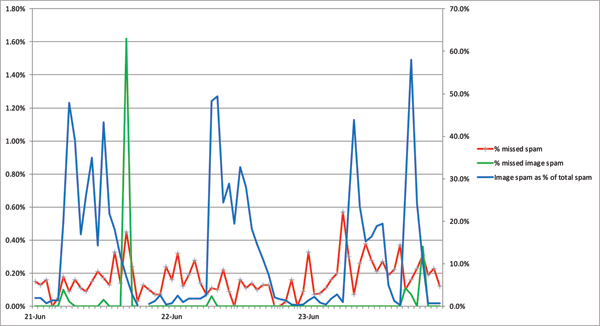
In the summary, we also looked at the spike in image spam, reported by Symantec and also noticed in our lab. We showed that image spam poses very little problems for spam filters: in fact, on average they had an easier time filtering it than other spam.