Posted by Virus Bulletin on Sep 11, 2014
Trick shows that spammers still try to beat content-based filters.
A decade ago, when spam had become a serious issue, most spam filters tried to block the unwanted emails based on their content. This resulted in a cat-and-mouse game between spammers and spam filters, with the former constantly looking for new ways to obfuscate the content of their messages.
To help those developing spam filters, anti-spam researcher John-Graham Cumming (now Programmer at CloudFlare, and a member of VB's advisory board) put together the Spammers' Compendium: an overview of tricks used by spammers to confuse filters. Since 2008, Virus Bulletin has hosted the Spammers' Compendium.
These days, spam filters look at far more than just the content of the email and not without success: as we have regularly pointed out in our vbspam tests, spam filters have become pretty good at filtering spam.
However, content filtering is still taking place and spammers are still using obfuscation techniques. Brian Bebeau, a researcher at Trustwave spotted a spam that used left-to-right override (LTRO) to obfuscate the text in a phishing email.
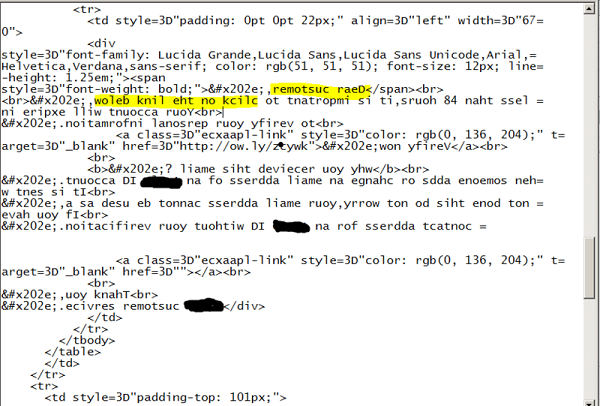
LTRO and its sibling RTLO are unicode characters used to reverse the order of the text from left-to-right to right-to-left and vice versa, making them useful in bidirectional text that combines various alphabets.
It has been occasionally used in malware to hide the file extension, thus making a user believe they are opening a harmless file type. I was intrigued to learn that spammers had now picked up this trick too.
Then I dug a little deeper and found that the Spammers' Compendium actually records the use of RTLO in spam as early as 2005. Still, I thought this use — which uses full sentences rather than a few characters — different enough to update the entry.
Meanwhile, at the Word to the Wise blog, Laura Atkins wrote a post on the various parts of the email content spam filters look at these days.
Posted on 11 September 2014 by Martijn Grooten