Posted by Virus Bulletin on Sep 3, 2014
Aditya K. Sood and Rohit Bansal dissect botnet primarily used for financial fraud.
It is unlikely that anyone still thinks that cybercrime is performed by 16-year-old kids who write short pieces of code that wreak havoc all over the world, but if you do still hold that belief, it won't hurt to take a look behind the scenes of a modern botnet operation. Today's botnets show how cybercrime has become a professional 'industry' in which many tactics seen in the legitimate e-commerce and IT service industries are deployed.
Today, we publish the first part of a paper by security researchers Aditya K. Sood and Rohit Bansal, in which they take a close look at the 'Citadel' botnet.
Citadel, a descendant of 'Zeus', is primarily used to conduct financial fraud by performing hidden transactions from a victim's online banking systems. It is sold in the underground community as part of a number of crimeware services packages.
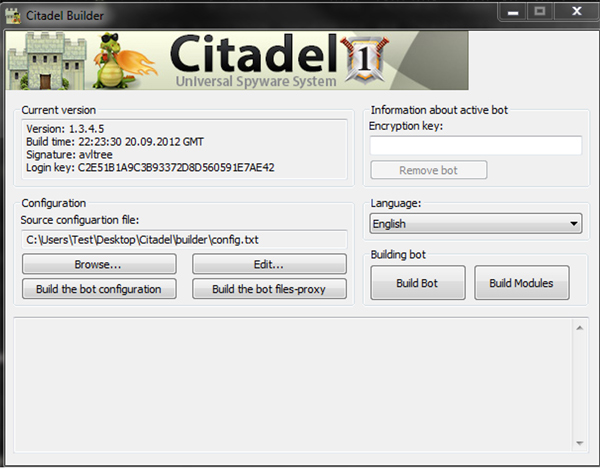
In the first part of their paper, Aditya and Rohit look at the design and implementation of Citadel. They study the builder kit, used to build the bot once a victim's computer has been infected, as well as the encryption used for command and control communication. The latter clearly shows some 'improvements' compared to the original Zeus code.
In this first part, the researchers also look at the admin panel, which Citadel's 'customers' use to control the individual bots, and at the various modules the botnet supports (from keyloggers to web injects), thus allowing the botnet to be tailored to a customer's specific needs.
The paper can be read here. The second part, in which the researchers perform both static and dynamic analysis of the botnet code, will be published next week. A PDF of the full paper will also be published next week.
Aditya and Rohit have written several VB article in the past. Now that you can access such articles for free, why not read their study of the 'NiFramer' injector or their analysis of the 'Styx' exploit pack.
Posted on 03 September 2014 by Martijn Grooten