Posted by Virus Bulletin on Sep 2, 2014
Hong Kei Chan and Liang Huang describe the various aspects and the evolution of point-of-sale malware.
In the weeks running up to VB2014 (the 24th Virus Bulletin International Conference), we are looking at some of the research that will be presented at the event. Today, we look at the paper 'Swipe away, we're watching you', by Fortinet researchers Hong Kei Chan and Liang Huang.
We Europeans will see many familiar names among the local shops when we travel to Seattle: retail chain Target, crafts store Michaels, department store Neiman Marcus, fast-food restaurant Dairy Queen, Asia-themed restaurant P. F. Chang. Names that are all familiar from the recent security news: they have all suffered data breaches via their payment terminals in the past year.
Point-of-sale (PoS) malware has existed for more than half a decade, but the aforementioned data breaches have made it a prime concern for retail CTOs and CFOs alike. Only a few weeks ago, US-CERT issued an advisory about 'Backoff', yet another kind of PoS malware (analysed by SpiderLabs here). Cybercriminals have always gone where the money is; by targeting PoS terminals, they are able to obtain very many credit card numbers at once.
In the first part of their paper, Kei and Liang take a bird's-eye view of PoS malware and describe the three stages of a typical PoS malware attack.
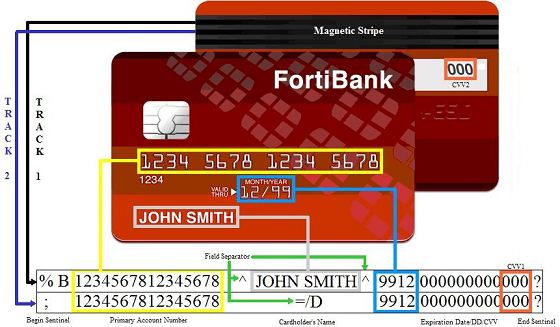
First, the malware reads raw memory data into buffers. While for the terminal to be PCI compliant, the credit card data needs to be encrypted before being transmitted over the Internet, for a short period the numbers are stored unencrypted in volatile memory.
This raw memory data contains a lot of noise and in the second stage of the attack, the PoS malware uses a number of methods to filter card numbers and other relevant data from this noise.
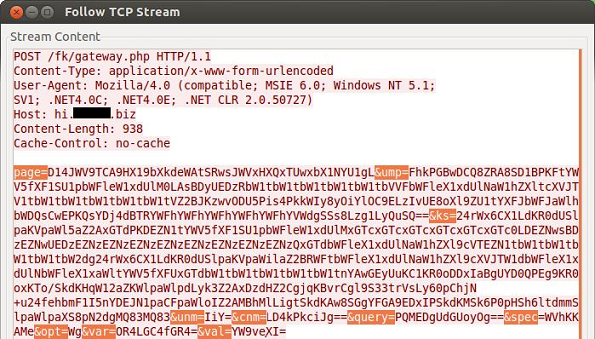
Finally, the data is sent to a command and control server, often encrypted and sometimes even using Tor, using techniques not dissimilar to what those seen in malware targeting home and office PCs.
In the second part of the paper, the authors zoom in one on particular PoS malware family, 'Dexter', and show how it has evolved over time.
From a relatively basic version with a compilation date of March 2011, to the most recent version ('Misto'), first compiled at the beginning of 2014, the paper shows in great detail how Dexter has evolved over time. For instance, earlier versions of the malware would search the memory of all but a few 'blacklisted' processes, while Misto only parses memory of a few targeted processes.
However, Misto doesn't have all the features of its predecessors (for instance, it lacks a keylogger), giving the authors cause to wonder if it has been branched off from an early version of Dexter.
The fact that credit card payments can be checked in real time over the Internet has proved very useful for smaller and larger shop owners alike. However, this also provide criminals with a new attack vector which, especially when cards lack EMV ('Chip-and-PIN'), they are all too eager to exploit.
In their presentation, Kei and Liang will include a live demonstration of PoS-malware in action.
Registration for VB2014 is still open.
Posted on 02 September 2014 by Martijn Grooten