Posted by Virus Bulletin on Sep 22, 2014
Jérôme Segura looks at recent developments in malicious cold calls.
In the weeks running up to VB2014 (the 24th Virus Bulletin International Conference), we are looking at some of the research that will be presented at the event. Today, in the final entry in this series, we look at the paper 'Tech Support Scams 2.0: an inside look into the evolution of the classic Microsoft tech support scam' , by Jérôme Segura (Malwarebytes).
Two years ago, at VB2012 in Dallas, I co-presented a paper on tech support scams. Somewhat naively, I expected the scams to die out before too long: soon, enough people would know not to trust people calling about computer issues that the scam would stop being profitable to the scammers.
I couldn't have been more wrong, and no one knows this better than Jérôme: on the Malwarebytes blog, he has written many posts about his adventures with support scammers. Adventures which tend to be quite hilarious - until one realises that real people continue to fall victim to such scams.
In his paper, Jérôme explains how the scam has evolved: not only do many callers no longer claim they are calling on behalf of Microsoft, they have also broadened their scope, and apart from Windows are now also targeting Mac and Android users.
Scammers continue to find inventive ways to 'prove' something is wrong with the victim's computer or device, such as a failing ping to protection.com (a domain that doesn't accept ICMP requests) or the 'ESTABLISHED' shown by the netstat command as a proof that bad guys are currently and actively stealing all your information.

In one instance, the scammers used a Netflix phishing page which gave a login error (but allowed the crooks to steal the credentials) and urged the victim to call a phone number, upon which they would be told that their computer had been hacked - something that could only be fixed after paying a hefty fee.
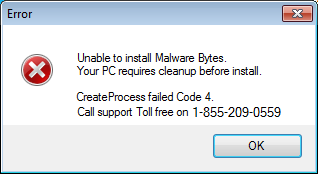
Support scams continue to evolve, and in his presentation, Jérôme will talk about a number of recent developments that occurred after he submitted the paper. These include scammers claiming to be the official support technicians of various security products (something that no doubt will be of interest to many attendees), as well as further evidence of scams operating from within the US itself.
The paper finishes with a number of useful suggestions for those who, like Jérôme, want to gather intelligence on support scammers. Many will not want to go as far as the Metasploit researcher who released a zero-day exploit in Ammyy, a remote access tool popular among scammers, with the purpose of 'fighting back'. However, there are other, less ethically dubious ways to gather intelligence on these scams and the tactics used; they will help prevent people from falling victim.
VB2014 takes place next week in Seattle. Registration for VB2014 is still possible.
Posted on 22 September 2014 by Martijn Grooten