Posted by Virus Bulletin on Oct 22, 2014
Luis Corrons dives into the world of shady Android apps.
Over the next few months, we will be sharing VB2014 conference papers as well as video recordings of the presentations. Today, we have added 'Exposing Android white collar criminals' by Panda Security researcher Luis Corrons.
Android is by far the most popular operating system when it comes to mobile malware, and it isn't surprising that this year's conference programme included a number of talks on the tricks used by Android malware to infect devices.
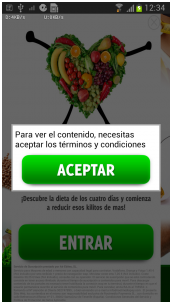
But not all malicious apps need to use such tricks: Luis Corrons discussed various apps that use social engineering to subscribe the victim to premium rate SMS services. In many cases, the methods used are verging on legal - for instance, an app that requires the user to accept its terms and conditions, which openly state its purpose, but in a very small font.
Other apps stray from the line of legality a little more, for instance by presenting a web page designed to trick users into believing it is the official Google Play store, or by claiming to be the official app of a popular brand.

Despite the fact that it wasn't hard to find out who was behind these pieces malware, Luis said that getting those people prosecuted wasn't easy - if possible at all.
You can read Luis's paper here in HTML-format, or download it here as a PDF (no registration or subscription required).
Posted on 22 October 2014 by Martijn Grooten