Posted by Virus Bulletin on Oct 8, 2014
Raul Alvarez studies cavity file infector.
Most file infectors increase the length of the infected file, as the malicious code is added as a new section of the host file, or to the last section of that file. 'Cavity' file infectors are different though: they infect files without increasing their size.
Today, we publish a paper by Raul Alvarez, a researcher for Fortinet, in which he studies Win32/Huhk, a virus that implements cavity file infection.
In the paper, Raul explains what happens when an infected file is run, as well as how other files are being infected. Huhk is polymorphic in nature, something which is achieved through a simple XOR operation with a one-byte key.
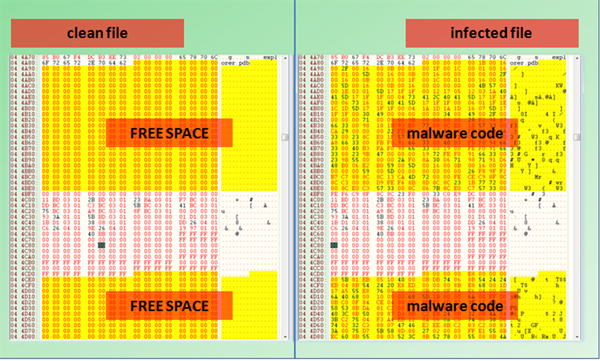
Of course, the virus needs to find a way to hide in the host file without affecting the latter's ability to run. To this end, Huhk looks for continuous memory locations filled with zeros. If the total size of such locations is greater than 7,005 bytes, it is able to infect the file.
You can read the paper here in HTML format or here as a PDF.
If you like this paper, you will probably like two other papers by Raul we published recently: Bird's Nest (on Neshta) and API-EPO (on W32/Daum).
Posted on 08 October 2014 by Martijn Grooten