Posted by Virus Bulletin on Oct 15, 2014
Users and administrators urged to stop supporting the protocol, or at least to prevent downgrade attacks.
After Heartbleed and Shellshock, or the SSL/TLS attacks CRIME and BEAST, 'POODLE' does sound rather cute. Yet the vulnerability in version 3.0 of the SSL protocol that was disclosed by Google researchers yesterday is fairly serious and shouldn't be ignored.
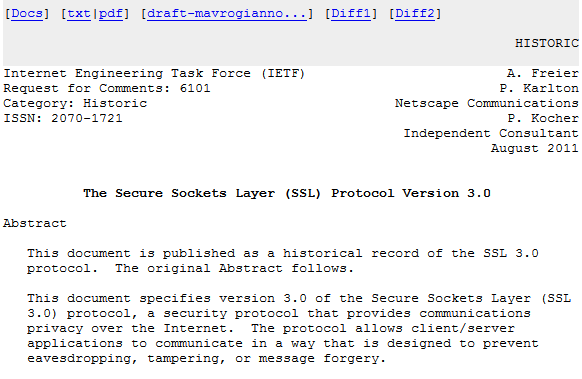
Details on POODLE, which stands for 'Padding Oracle On Downgraded Legacy Encryption', were shared in a document on OpenSSL's website (PDF), but it is important to note that the vulnerability is in the protocol rather than in the implementations, and other implementations of SSL 3.0 are just as vulnerable. Microsoft, for instance, published an advisory here.
The vulnerability has to do with the way SSL 3.0 handles padding: adding characters to a plaintext to make its length an integral number of blocks, which is necessary in order to make cipher-block chaining (CBC) work. Technical details on the vulnerability and how it can be attacked - both of which require some basic understanding of cryptography - have been posted by, among others, Adam Langley, Matthew Green and Daniel Fox Franke.
The good news is that there is a replacement for SSL 3.0. It is called TLS and has been available since 1999. There are very few clients and servers that do not support it (Internet Explorer 6 is a notable exception).
The bad news is that an attacker who finds himself in a man-in-the-middle position may be able to 'downgrade' the connection, making both ends use the vulnerable protocol, even though they both support TLS 1.0 or later.
The easiest way to fix this vulnerability is simply to disable SSL 3.0 support in all clients and servers you manage. If for some reason that is not possible, Google recommends supporting TLS_FALLBACK_SCSV, which prevents downgrade attacks. Yesterday, OpenSSL released a patch that adds support for TLS_FALLBACK_SCSV.
Of course, SSL/TLS isn't only used for securing HTTP connections. However, as POODLE requires an attacker to force the target to make a very large number of specific connections, the ability for the attacker to use it on other protocols seems all but impossible.
Still, one never knows, and there is always the possibility for the attack to be improved now that it is public. Johannes Ullrich explains how to turn off SSL 3.0 in various commonly used clients and servers.
Backwards compatibility is a good thing and makes the Internet work even for those who, for various reasons, aren't able to use the latest software and protocols. But eventually, we will have to stop supporting outdated protocols. For SSL 3.0, that time has come.
Posted on 15 October 2014 by Martijn Grooten