Posted by Virus Bulletin on Oct 31, 2014
Malicious apps may have more privileges than security software.
There are many people without whom a Virus Bulletin conference wouldn't be possible: the VB team, the crew from Cue Media, the hotel staff, the speakers, the sponsors, the delegates. But the unsung heroes of a conference are the reserve speakers.
They prepare a presentation just like other speakers, but know they might never deliver it - and they have to be available throughout the conference just in case a speaker cancels at the last minute. This year, K7 Computing researchers Samir Mody and Dhanalakshmi V were in just that position and, while we were glad that the scheduled speakers all turned up, the down side was that we didn't get to hear Samir and Dhanalakshmi's presentation.
They had prepared a paper on early launch Android malware: malicious apps that run with more privileges than security software (something that Google has now admitted is a problem).
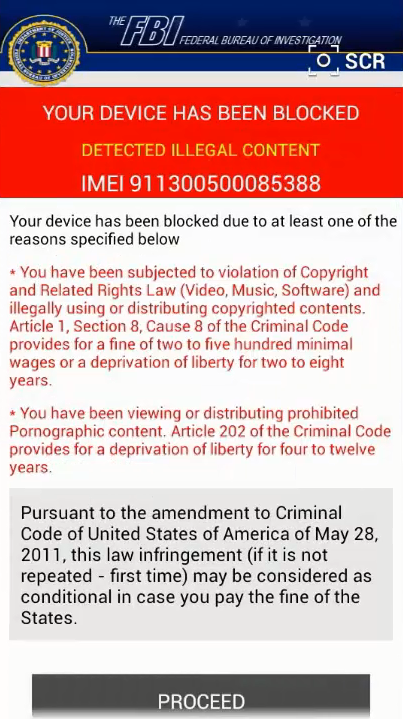
They focused in particular on the 'Koler' ransomware, which made the news this week for having added worm-like capabilities. In a short demo, they were going to show how an anti-virus product detected Koler as it was about to be installed but that, should a user have installed it anyway, it would block any attempt by the user to uninstall it.
To improve this less-than-optimal situation, Samir and Dhanalakshmi proposed an updated boot and broadcast framework that would enable trusted applications such as mobile security apps to launch before any other application.
We have uploaded both the presentation slides and the demo to our YouTube channel.