Posted by Virus Bulletin on Nov 24, 2014
Nation state likely behind campaign that goes back many years.
Few terms are misused in a security context as often as the term 'advanced', perhaps in part because the industry doesn't like to admit that most of the threats we're facing aren't particularly advanced. Yet for the 'Regin' espionage tool, which Symantec wrote about yesterday, it seems fully justified.
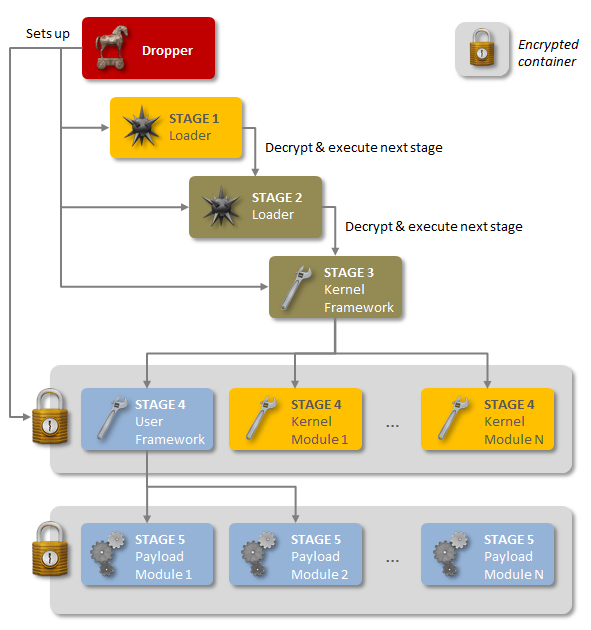
Regin has been used in espionage campaigns since at least 2008. It is a multi-staged threat (like Stuxnet) that uses a modular approach (like Flame), thus placing it among the most advanced threats ever detected.
Though the campaign has only recently been discovered, individual components of Regin have been analysed in the past - for example, F-Secure researcher Antti Tikkanen writes about how his company analysed a malicious driver belonging to the same campaign in early 2009.
There have been victims in many countries, but just over half of the confirmed infections occurred either in Russia (28%) or in Saudi Arabia (24%). Interestingly, almost half of the confirmed infections affected what Symantec refers to as 'private individuals and small businesses'.
Attribution is hard, and Symantec is right to refrain from making guesses about where the actors behind Regin are based. However, given the resources required to build and maintain such a tool, and the fact that Regin's purpose appears to be the gathering of intelligence, the company believes that a nation state is behind it.
More details can be found in a whitepaper (pdf) published by Symantec.
Kaspersky Lab has also published an analysis of Regin. As well as adding more technical details, and the fact that victims were found on the pacific island nations of Fiji and Kiribati, the Kaspersky researchers also report that a large GSM operator was among the targets.
One victim is named explicitly: Belgian cryptography professor Jean-Jacques Quisquater, who is an expert on smartcard encryption. Earlier this year, Quisquater said that he had been the victim of a spear-phishing attack, which he blamed on 'the NSA and/or GCHQ'. Many (myself included) believed that Quisquater might have mistaken an ordinary attack for something more serious. It now appears that Quisquater was right - at least about the seriousness of the threat.
Posted on 24 November 2014 by Martijn Grooten