Posted by Virus Bulletin on Nov 6, 2014
Terry Zink presents case study in which he describes setting a DMARC policy for Microsoft.
Over the next few months, we will be sharing VB2014 conference papers as well as video recordings of the presentations. Today, we have added 'DMARC - how to use it to improve your email reputation', by Microsoft's Terry Zink.
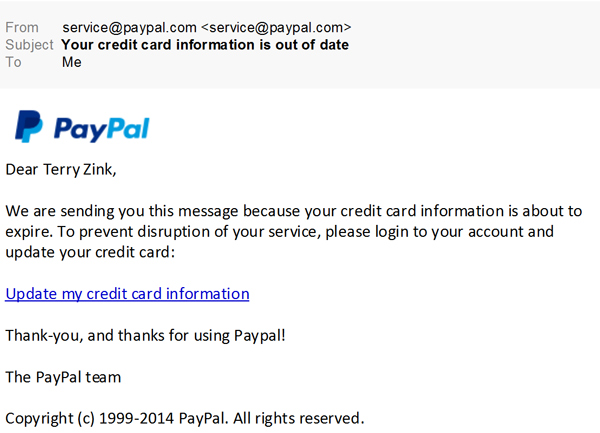
Email is a 30-year-old protocol, designed at a time when the Internet was much smaller and you could basically trust anyone. As a consequence, spammers and phishers can easily send email claiming to be someone else.
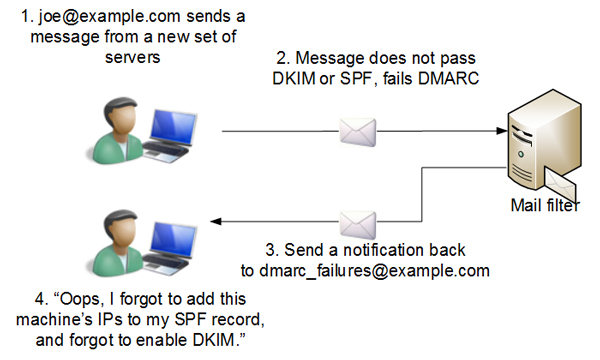
DMARC, which builds on both SPF and DKIM, attempts to solve that problem, at least partially, by giving senders a way to inform receivers which emails that claim to come from them really did come from them.
In his VB2014 Paper, Terry explains how DMARC works and how it helps to prevent phishers abusing domains that use the standard.
However, he also explains that DMARC is no silver bullet: if PayPal doesn't control the domain 'paypai.com', it can't stop phishers from using it. Moreover, as I wrote when Yahoo! and later AOL felt forced to set a strict DMARC policy, doing so can cause collateral damage.
Perhaps most interesting is the case study Terry presents in setting a DMARC record for Microsoft. The large company has many different business units that each send email, making setting a single DMARC record a far from trivial task. However, DMARC provides a mechanism whereby feedback from receivers can be used to detect incorrect or incomplete records, which in the end helped Terry set a fairly strict DMARC policy for the company.
You can read Terry's paper here in HTML-format, or download it here as a PDF (no registration or subscription required). You can download the presentation slides here. We have also uploaded the presentation to our YouTube channel.
For another introduction into DMARC, you can read the VB article John Levine wrote in March 2012, shortly after the standard was launched.