Posted by Virus Bulletin on Nov 26, 2014
What do your IP packet sizes say about whether you're a spammer?
Over the next few months, we will be sharing VB2014 conference papers as well as video recordings of the presentations. Today, we have added 'Labelling spam through the analysis of protocol patterns' by Bitdefender researchers Andrei Husanu and Alexandru Trifan.
Machines sending spam tend to behave differently in a number of ways from those sending legitimate emails. One of the ways people have long been fighting spam is to detect this difference, for instance by fingerprinting the TCP/IP connection to determine the operating system, or to check whether the sender starts 'talking SMTP' before the spam filter has sent the SMTP banner.
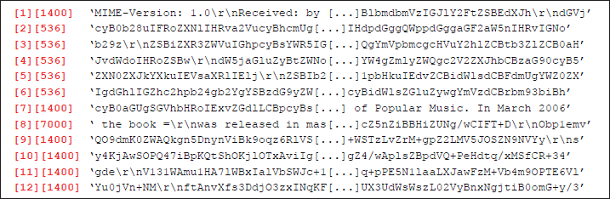
In their VB2014 paper, Andrei Husanu and Alexandru Trifan suggest a different way to distinguish spammers from legitimate emailers: they looked at the IP packet sizes of SMTP connections and found some behaviour that was typical of spammers trying to send a variation of the same message to as many recipients as possible, or of spam sent from a (likely compromised) mobile device.
You can read the paper here in HTML-format, or download it here as a PDF (no registration or subscription required). You can download the presentation slides here. We have also uploaded the presentation to our YouTube channel.
We apologise for the poor quality of the screen capture in the video. We will try to upload a better version at a later stage.
Posted on 26 November 2014 by Martijn Grooten