Posted by Virus Bulletin on Nov 21, 2014
Dhia Mahjoub explains how the topology of the AS graph can be used to uncover hotspots of maliciousness.
Over the next few months, we will be sharing VB2014 conference papers as well as video recordings of the presentations. Today, we have added 'Sweeping the IP space: the hunt for evil on the Internet' by OpenDNS researcher Dhia Mahjoub.
The Internet is often described as a network of networks. These individual networks are called Autonomous Systems (AS): collections of IPv4 and IPv6 network prefixes administered by the same entity and sharing a common routing policy. Each AS is identified by an Autonomous System Number (ASN).
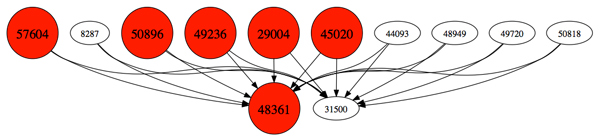
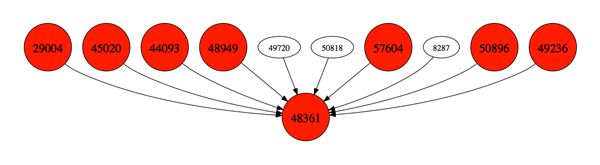
Together, the ASNs form the AS graph: a directed graph that links ASNs to their upstream counterparts. In his VB2014 paper, Dhia explains how this graph can be used to detect ASNs whose IP addresses host malicious content.
Traditionally, this is done by deriving scores based on content hosted, but by studying the ASN graph it is possible to show interconnections between ASNs and thus find IP ranges that are likely to be hosting malicious content - sometimes even before there are domains pointing to the IP addresses.
In his presentation, Dhia showed five use cases of this new way of exploring the IP space for maliciousness: from sibling ASNs all found to be hosting the same malicious content, to pre-emptively detecting malicious subdomains injected under compromised domains.
You can read the paper here in HTML-format, or download it here as a PDF (no registration or subscription required). We have also uploaded the presentation to our YouTube channel.