Posted by Virus Bulletin on Nov 4, 2014
Santiago Pontiroli takes us on a rollercoaster ride through cryptocurrency land.
Over the next few months, we will be sharing VB2014 conference papers as well as video recordings of the presentations. Today, we have added 'Well, that escalated quickly. From penny-stealing malware to multi-million-dollar heists, a quick overview of the bitcoin bonanza in the digital era', by Kaspersky's Santiago Pontiroli.
Today's gold rushes don't take people to California or Yukon. Rather they take place on the Internet, where people are mining bitcoins and related cryptocurrencies, sometimes getting very rich in the process, and occasionally losing a lot of money through bugs and blunders.
In his paper, Santiago Pontiroli takes us through the recent history of Bitcoin and the various aspects that matter for computer security. Watching his presentation at VB2014 was akin to a rollercoaster ride. On the one hand, cryptocurrencies are rather exciting — Santiago explained how many people in Latin America see Bitcoin as a way to defeat the deflation their economies are struggling with. On the other hand, it was hard not to feel dizzy and somewhat overwhelmed by the security issues and implications.
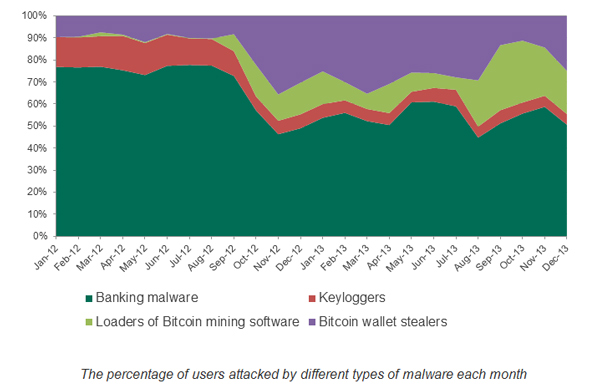
Malware targeting Bitcoin wallets or using other people's resources to mine for cryptocurrencies are perhaps the least of our worries. What about virus code (or worse, child abuse material) ending up in the blockchain? Or the common flaw of transaction malleability? Or the almost existential threat of the "51% attack"?
Cryptocurrencies are here to stay, but they come with their own unique set of problems that we cannot ignore. As Santiago concluded in his presentation, we're not in Kansas anymore.
You can read Santiago's paper here in HTML-format, or download it here as a PDF (no registration or subscription required). You can download the presentation slides here. We have also uploaded the presentation to our YouTube channel.
If you are interested in malware focusing on Bitcoin, make sure you read an article we published last year from another VB2014 speaker, Fortinet researcher Micky Pun, in which she studies several malware families engaged in Bitcoin mining.