Posted by Virus Bulletin on Nov 20, 2014
40 out of 48 tested products earn VB100 award.
If you follow the security news, you may believe that all you have to worry about are nation states using zero-day vulnerabilities to infiltrate networks and computers with stealth malware.
The reality is, of course, more complicated, and if this is indeed your biggest worry, your systems are exceptionally well secured. In practice, a malicious link is easily clicked, a malicious download easily mistaken for a legitimate one, and a patch easily missed. Hence anti-virus remains as important a layer of defence as ever.
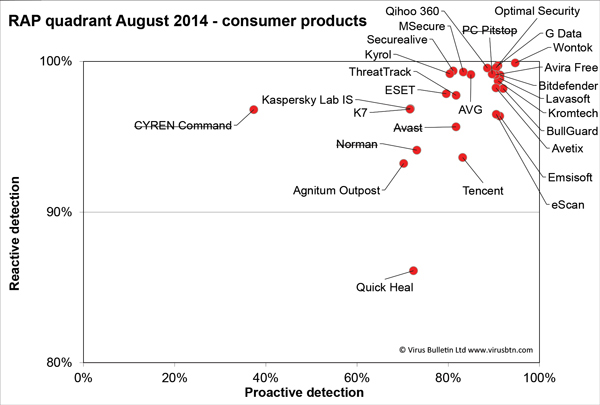
To find out which products are up to the job, John Hawes and his team tested no fewer than 48 products on Windows 8.1, the latest version of Microsoft's flagship operating system. 14 of these were classified as corporate products, with the remaining 34 designed to be used by consumers.
All corporate products, and all but eight consumer products performed well enough to achieve a VB100 award, demonstrating that, in their default state, they were capable of detecting all malware from the WildList without erroneously alerting on files from a 'clean set' of legitimate files.
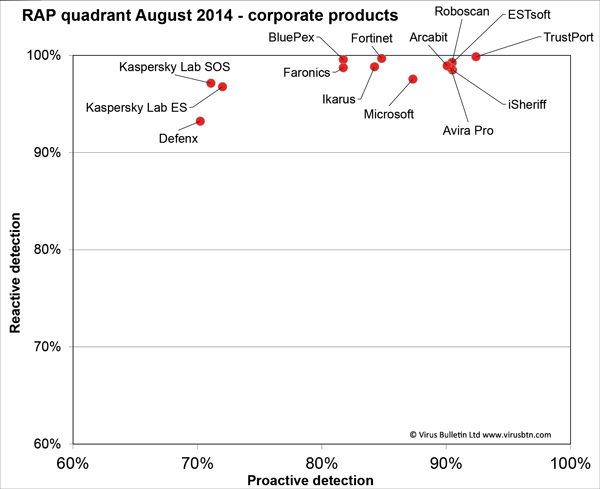
Products from the following vendors achieved a VB100 award: Agnitum, Arcabit, Avetix, AVG, Avira, Bitdefender, BluePex, BullGuard, Check Point, Defenx, Emsisoft, eScan, ESET, ESTsoft, Faronics, Fortinet, G Data, Ikarus, iSheriff, K7, Kaspersky Lab, Kingsoft, Kromtech, Lavasoft, Microsoft, Optimal Software, Panda, Qihoo 360, Quick Heal, Roboscan, Tencent, ThreatTrack, Total Defense, TrustPort, ULIS and Wontok.
The full report contains many other performance metrics and detailed information on each participating product, such as its recent test history and the stability of the product. As always, we encourage readers to read beyond the passes and the fails and study the full report, or consult the recent test history on our website.
The VB100 review can be viewed here in HTML format, or downloaded here as a PDF (no registration required).
If you are interested in submitting your product for future tests, or want to make use of our consulting opportunities, please don't hesitate to contact John Hawes at [email protected].
Posted on 20 November 2014 by Martijn Grooten