Posted by Virus Bulletin on Jan 6, 2015
See which anti-malware and anti-spam solutions achieved certification.
Shortly before the Christmas holidays, we published a new VB100 anti-malware test report as well as a new VBSpam test report.
John Hawes and his team put 29 anti-malware solutions through their paces on Windows Server 2008 and, for the first time ever on a Windows platform, all participating products achieved a VB100 award.
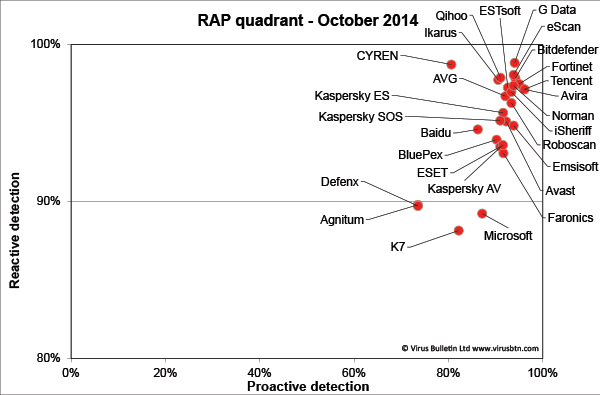
The full test report can be read here, or click here for a summary of the results.
There was almost a clean sweep in the latest VBSpam test as well, with only one product failing to achieve certification. However, while there were five VBSpam+ awards and nine 'ordinary' VBSpam awards, most products saw a slight drop in performance compared with the last few tests.
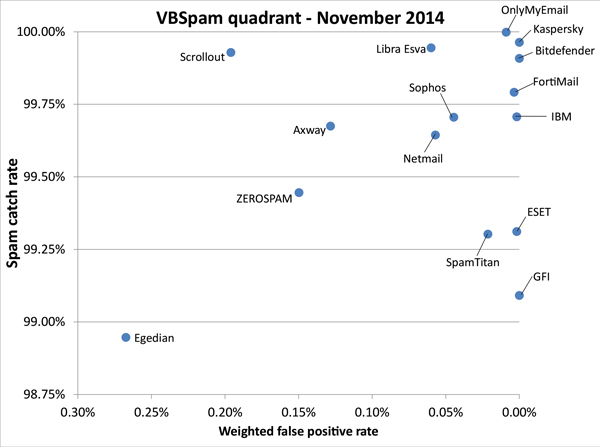
The full test report, which also looks at the products' performance throughout 2014, can be read here, or click here for a summary of the results.
Posted on 06 January 2015 by Martijn Grooten