Posted by Virus Bulletin on Jan 20, 2015
Raul Alvarez unwraps the many layers of an increasingly prevalent banking trojan.
Banking trojans remain one of the most prevalent kinds of malware. Among them, trojans based on Zeus have long been the most prevalent, but in recent months a relatively new trojan has been challenging the reign of Zeus: Vawtrak.
Also known as Neverquest or Snifula, Vawtrak initially targeted users of Japanese banking systems, but it has since broadened its scope. In a recent paper (pdf), Sophos researcher James Wyke looked at the malware's infection vector, as well how it targets banks and other financial institutions.
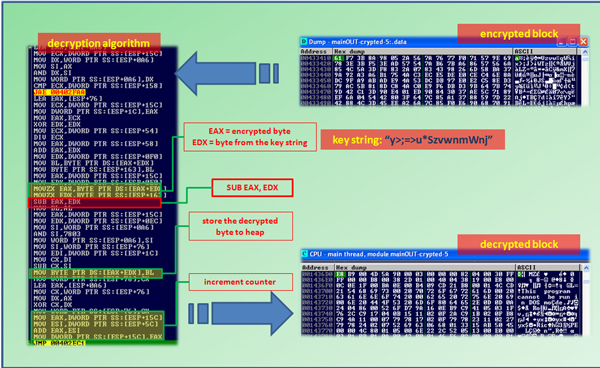
Today, we publish a paper by Fortinet researcher Raul Alvarez, in which he takes a close look at the malware itself. Like a Russian Matryoshka doll, it consists of multiple layers, with each layer (or doll) containing the next one until the final layer contains a malicious DLL.

In his paper, Raul takes us through the various layers and explains how each layer contains various tricks to frustrate researchers and debuggers alike. This not only makes it an essential read for anyone studying Vawtrak, but also a good introduction to modern malware analysis, which is very much about distinguishing real from bogus instructions and avoiding traps laid out for researchers.
You can read the paper here in HTML format or here as a PDF. Remember that all content published by Virus Bulletin can be read free of charge, with no registration required.
If you like this paper, be sure to read previous articles Raul wrote for Virus Bulletin, including analyses of W32/Huhk and the Neshta file infector.
Posted on 20 January 2015 by Martijn Grooten