Posted by Virus Bulletin on Feb 5, 2015
CVE-2015-0313 used in the wild as long ago as December.
Adobe has just issued an out-of-band patch for its Flash Player to fix a zero-day vulnerability that is actively being exploited in the wild.
You may be forgiven for thinking you had already patched this two weeks ago when Flash Player version 16.0.0.287 fixed CVE-2015-0310, or last week when version 16.0.0.296 fixed CVE-2015-0311, another vulnerability that was being used in exploit kits in the wild.
This, however, is yet another vulnerability: CVE-2015-0313, which is being used against Internet Explorer and Firefox users.
This time it is not the Angler exploit kit that is infecting users, but the relatively unknown 'Hanjuan' kit, as Trend Micro reports. A number of researchers, including F-Secure's Timo Hirvonen, believe that Hanjuan's use of the vulnerability may go back as far as December last year.
It seems Flash zero-day CVE-2015-0313 might have been exploit by HanJuan exploit kit already on 2014-12-20 or even earlier...— Timo Hirvonen (@TimoHirvonen) February 3, 2015
CVE-2015-0313 is a use-after-free vulnerability in Flash's handling of fast memory access to 'domain memory'. SpiderLabs's Ben Hayak has analysed the vulnerability here, with Trend Micro's Peter Pi providing another analysis here.
Last week, we published the VB2014 paper 'Ubiquitous Flash, ubiquitous exploits, ubiquitous mitigation' from Microsoft researchers Chun Feng and Elia Florio. This paper analyses two earlier vulnerabilities in Flash Player's implementation of domain memory opcode and also serves as a good general introduction to the subject. You can read their paper here in HTML-format, or download it here as a PDF.
While updating to Flash Player version 16.0.0.305 should be given the highest priority, users might also want to consider making Flash click-to-play in all their browsers. Unlike NoScript, which does the same to JavaScript, it doesn't seriously impact the browsing experience. Graham Cluley explains how to enable this feature in the five most popular browsers.
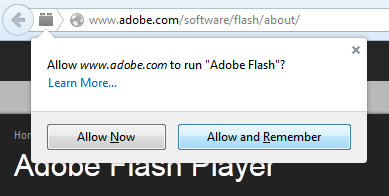
By making Flash Player click-to-play, even Adobe can't run Flash without your permission.
Posted on 05 February 2015 by Martijn Grooten