Posted by Virus Bulletin on Feb 25, 2015
Each discovered vulnerability is actually a good news story.
Last week, security firm GFI published some research in which it looked at the number of vulnerabilities reported last year, their severity, and which operating systems they affect.
The surprising result is that Apple's OS X and iOS lead the table, followed by the Linux Kernel, each of which saw significantly more vulnerabilities patched last year than any Windows version.
However, this paints a rather incomplete picture of the current security landscape. I can't put it more eloquently than VB's John Hawes, who spoke to Softonic on the issue:
"Basically it's like staring at a bunch of garden walls to see how many footballs come flying over the top — it doesn't say much about the height or quality of a given wall, but maybe something about how many people are on the other side and what kind of games they're playing."
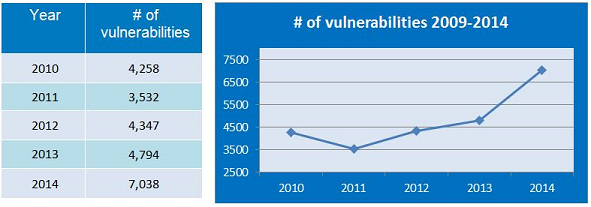
But there's another interesting point to note: there was a significant increase in the total number of vulnerabilities discovered - an increase of almost 50%.
It is tempting to see this as bad news. After all, each vulnerability provides an attacker with another means of gaining access to unpatched systems.
Yet we shouldn't forget that all those vulnerabilities were present before they were disclosed; in some cases they had been there for more than a decade. We know that some of the more than 7,000 reported vulnerabilities were known to attackers and were being exploited, and it's very likely that there are also cases that we're not aware of. Hence we should really read this as more than 7,000 security success stories.
Indeed, some serious efforts have been made to encourage the discovery and responsible disclosure of vulnerabilities: from an increasing number of bug bounty programs to Google's Project Zero and the funding for critical open-source projects in the wake of Heartbleed.
Only a very naive person would believe that we have now discovered the majority of vulnerabilities in existence and that new ones aren't being introduced into products any longer. Thus the best we can hope for is that more vulnerabilities will be discovered and disclosed quickly. Here's to passing the 10,000 mark this year!
Posted on 25 February 2015 by Martijn Grooten