Posted by Virus Bulletin on Feb 5, 2015
Wei Xu and his colleagues attempt to block domains before they're used for bad purposes.
Since the close of the VB2014 conference in Seattle in October, we have been sharing VB2014 conference papers as well as video recordings of the presentations. Today, we have added 'We know it before you do: predicting malicious domains' by Palo Alto Networks researchers Wei Xu, Yanxin Zhang and Kyle Sanders.
Whether they're used for command and control communication, to host malware or in a phishing campaign, malicious domains play an important role in today's threats. Security firms thus try hard to detect them and add them to their blacklists.
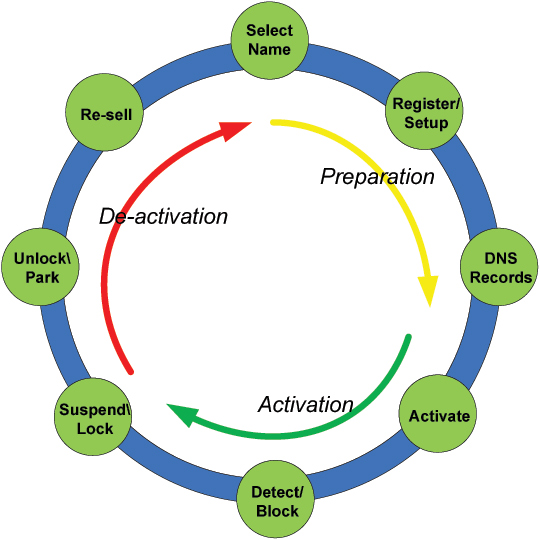
However, with domains being recycled quickly, a reactive approach might not be good enough. In their VB2014 paper, Palo Alto Networks researchers Wei Xu, Yanxin Zhang and Kyle Sanders describe how they tried to predict malicious domains.
They combine four different techniques: looking at known malicious domain names that are likely to be reused; looking at the domain names themselves to detect those generated by DGAs; looking at DNS queries made to the domains; and looking at connections between the domain names, such as shared DNS infrastructure.
Using these techniques and one month's data as input, they were able to predict almost 2,200 malicious domains, 83% of which were listed on VirusTotal as known malicious by at least one vendor. Passive DNS records showed that they predicted malicious domains an average of eight hours before DNS queries showed up in the PDNS feed.
You can read the paper here in HTML-format, or download it here as a PDF (no registration or subscription required). We have also uploaded the presentation to our YouTube channel.