Posted by Virus Bulletin on Feb 4, 2015
Many decent performances in VB's latest comparative spam filter test.
A decade ago, there were optimists who thought that the spam problem would soon be eradicated. At the same time, pessimists thought that spam would quickly become such a big problem that we'd all stop using email.
The bad news is that the optimists were wrong: the vast majority of email traffic sent these days is spam. The good news is that the pessimists were wrong too: spam is so well mitigated that billions of people still use email every day.
Spam filters — or email security solutions, as they are often called these days — aren't solely responsible for this mitigation, but they play a very important part, making them the unsung heroes of the email infrastructure. When they do their job well, spam filters keep inboxes tidy and prevent users from being tempted to open dodgy links or malicious attachments.
As the spam landscape evolves, so do spam filters. Or so one would hope. Since the spring of 2009, Virus Bulletin has been publishing bi-monthly reports on the performance of spam filters.
The most recent of these reports was published earlier this week. For most participating products there was good news: they bounced back from a relatively weak performance in the November 2014 test.
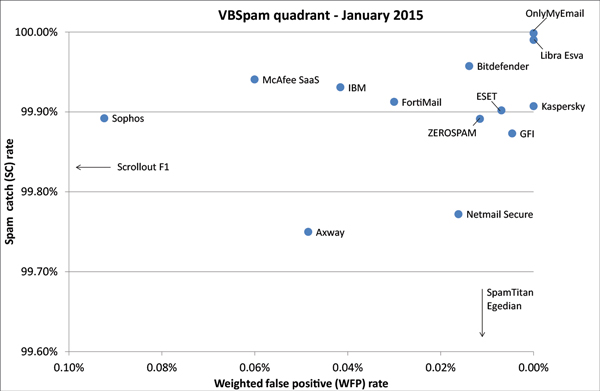
Thirteen products achieved the widely respected VBSpam award for their performance, and six of them — ESET, GFI, Kaspersky, Libra Esva, OnlyMyEmail and ZEROSPAM — even achieved a VBSpam+ award for blocking more than 99.5% of spam, while blocking no legitimate emails and very few newsletters.
For some products, however, the results were disappointing and their developers will be working hard to show that their poor performance was a one-off incident.
The full VBSpam report can be downloaded here in HTML format or here as a PDF. For an easier to digest version of the results, a summary of the report can be downloaded here in HTML format or here as a PDF.
Are you providing an email security solution whose performance you'd like to be measured by Virus Bulletin? Do not hesitate to email VB Editor Martijn Grooten at [email protected] or check out the details of our consulting services.
Posted on 04 February 2015 by Martijn Grooten