Posted by Virus Bulletin on Feb 13, 2015
Hexiang Hu used tool to detect Bladabindi backdoor.
The .NET framework is a popular way to write software. As applications built with the framework compile into a Common Intermediate Language (CIL), single binaries can run on multiple platforms and CPU architectures.
However, as is so often the case, what is useful for authors of benign software is also popular amongst malware authors. Indeed, several recent malware families have been developed using the .NET framework, often using complex packers to frustrate the analysis of code.
During his time as an intern at Microsoft, Hexiang Hu wrote a tool to assist in the automatic analysis of malware written using .NET. He presented this tool in his VB2014 presentation, in which he didn't shy away from the technical details.
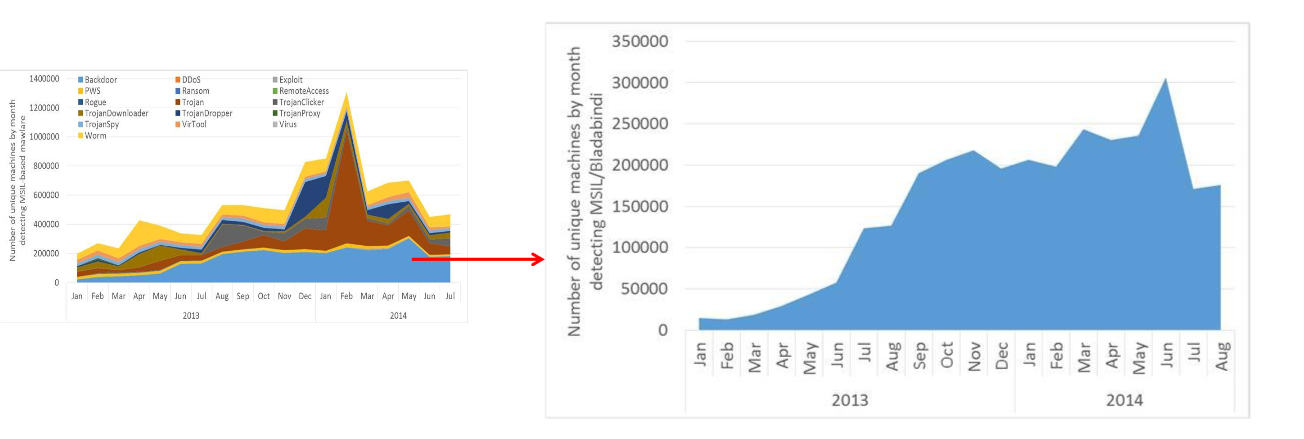
Hexiang also presented a case study in which the tool was used to detect the prevalent 'Bladabindi' backdoor, which was subject to a somewhat controversial legal action from Microsoft last year.
Because this was one of the event's 'last-minute' presentations, there was no written paper for us to publish. We have, however, uploaded the video to our YouTube channel. You can download the presentation slides here.