Posted by Virus Bulletin on Feb 11, 2015
Security vendors to receive alerts when legitimate files are detected as malicious.
False positives are a huge problem for the IT industry in general and for security products in particular. Indeed, in our VB100 and VBSpam comparative tests, many otherwise well performing products have failed to achieve an award because they blocked too many legitimate files or emails.
Yet in a time in which most detections are based on heuristics, mistakes are easily made. Thus it is good to know that the industry is working on various projects to prevent widely used software from being detected as malicious.
One of these projects is the 'Clean file Metadata eXchange' (CMX), the idea for which was first presented by Igor Muttik and Mark Kennedy in a VB2013 presentation and which is now available as part of the IEEE's Anti-Malware Support Service.
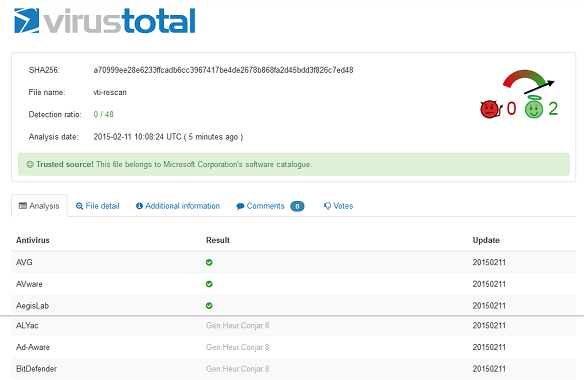
While the CMX is proactive and will help prevent anti-virus products from detecting clean files as malicious, VirusTotal has started a new project that aims to be reactive to the false detection of (large) software vendors' files.
The project, currently referred to by the (internal) name 'trusted source', allows large software houses to upload files in their catalogue. Should VirusTotal note that an anti-virus product detects one of these files as malicious, the vendor will receive an alert. The files are also tagged when shared with participating security products, to prevent these from adding detection.
The project has only been active for a week so far, and with only one software vendor, Microsoft, submitting files, but VirusTotal reports that it has already detected over 6,000 false positives.