Posted by Virus Bulletin on Mar 11, 2015
Microsoft patches .LNK vulnerability after 2010 patch was found to be incomplete.
Mention Stuxnet and you'll have many a security researcher's attention. The worm, which was discovered in 2010, used a number of zero-day vulnerabilities to reach its target: air-gapped Windows PCs at the Natanz nuclear plant in Iran. Most prominent among these was CVE-2010-2568, which allowed an attacker to execute remote code through a specially crafted .LNK file.
The vulnerability could be triggered by plugging an infected USB drive into a vulnerable PC, thus allowing an attacker to bridge air gaps. Researchers from Kaspersky have since found that the same exploit was used by the 'Equation Group' even before Stuxnet.
Microsoft patched the vulnerability in August 2010, but earlier this year researchers from HP's Zero Day Initiative discovered that the patch was insufficient and still left an attack surface open.
The vulnerability was privately disclosed to Microsoft, who in yesterday's Patch Tuesday release, patched this vulnerability, while HP published a lengthy blog post with full details on this new vulnerability. It has been assigned CVE number CVE-2015-0096.
Chances are you don't run a nuclear plant. That doesn't mean you shouldn't patch this vulnerability though: the original vulnerability is still widely used by malware to trick an unpatched Windows PC into executing malicious libraries.
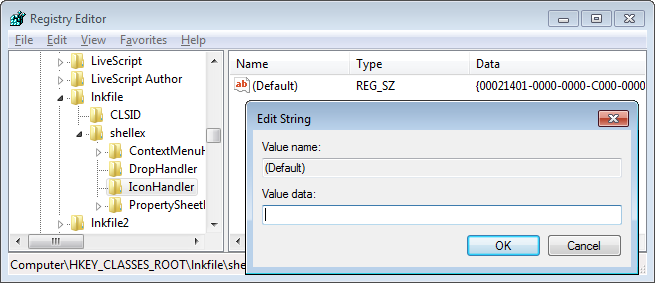
For the more paranoid, it is good to note that while the 2010 patch didn't fully solve the issue (and, speaking to Ars Technica, HP's Brian Gorenc said "it's hard to believe that somebody didn't know about this bug prior to it being patched today"), the workaround provided by Microsoft back in 2010 would have prevented further exploitation. It may still be a good idea to apply it on critical systems as its only impact is that shortcut icons will not be displayed.
This isn't the only reason to apply Microsoft's patches though: no fewer than five out of the 14 bulletins are rated 'critical', while another bulletin patches the FREAK vulnerability. For those who prefer their security information in audio format, Johannes Ullrich's excellent daily ISC Stormcast podcast provides a brief summary of the important issues.
On the subject of Stuxnet, I can't recommend Kim Zetter's book Countdown to Zero Day highly enough. I reviewed it for this blog last year.
Posted on 11 March 2015 by Martijn Grooten