Posted by Virus Bulletin on Apr 2, 2015
Chinese certificate authority told to re-apply.
When a web client, such as a browser, attempts to make an HTTPS connection, it needs to know that no man-in-the-middle attack is taking place. The web server therefore proves its authenticity by presenting the client with a certificate. This certificate is cryptographically signed by a certificate authority (CA), whose certificate is in turn signed by another CA until this chain reaches a CA whose public key is hard-coded in the browser or on the operating system.
This model is often said to be broken. After all, it only takes one root CA to trust an intermediate CA that doesn't check too carefully who is applying for certificates for someone to be able to perform a man-in-the-middle attack on encrypted Internet traffic.
Indeed, this happened recently when someone was able to register the email address [email protected] (live.fi is the Finnish version of Microsoft's live.com webmail offering) and use this to obtain a certificate for the domain. Thankfully, the certificate was only created to make a point.
In another recent story, Egypt-based MCS Holdings, an intermediate CA whose certificate was signed by China's CNNIC, created a number of certificates for Google domains. Although these domains were likely intended for internal tests, Google was understandably upset when it discovered the issue - explaining the situation in a blog post.
Now, in an update to its blog post, Google has effectively announced that it has suspended CNNIC from the root store of its Chrome browser.
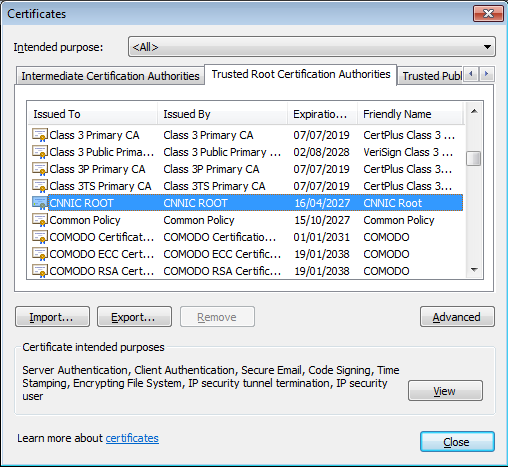
Cryptography doesn't 'do' suspensions. What Google will do instead is to remove the root certificate from the store and create a whitelist of CNNIC's existing certificates, to prevent users who rely on them from getting alerts about invalid certificates (alerts which are at the least very unwise to bypass). It is worth nothing that Chrome is a very popular browser in China.
Google has said that CNNIC is welcome to reapply once 'suitable technical and procedural controls are in place'. One of these controls is certificate transparency, which will help detect fraudulent certificates. CNNIC probably has little choice but to do so, despite calling Google's decision 'unacceptable and unintelligible'.
For MCS Holdings, though, this will come too late. Trust in its certificates has already been revoked by Mozilla and Microsoft. The company's own investigation - the first conclusion of which is that it is pretty awesome - certainly doesn't inspire confidence.
Though broken in a strict academic sense, the quick discovery of the rogue certificates and Google's further handling of the case shows that the CA model's error-correcting capabilities are actually pretty good. As such, the huge problems that exist in theory are, in practice, mitigated very well.
Posted on 02 April 2015 by Martijn Grooten