Posted by Virus Bulletin on Apr 28, 2015
Test process also uncovers job spam illustrative of trend.
Last week, we published our 36th comparative anti-spam test. All but one of the 16 participating full solutions achieved a VBSpam award, all blocking a large percentage of spam, while blocking very few legitimate emails.
Seven products — Bitdefender, ESET, GFI MailEssentials, Kaspersky LMS, IBM Lotus Protector, Libra Esva and Netmail Secure — achieved a VBSpam+ award for blocking more than 99.5% of spam, while generating no false positives at all in the 'ham' corpus, and very few false positives in a separate corpus of newsletters.

This test marks six full years of running VBSpam tests. Looking back over those six years, we notice that the problem of spam hasn't got any worse and remains well mitigated by a number of factors, from industry efforts to spam filters; the latter remain essential for any user of email.
We have also noticed a number of trends over the last six years. One of these is that an increasing amount of spam is being sent from compromised (web) servers, most of which run Linux. We have shown in the past how this kind of spam tends to be harder to block.
Another trend is an increased use of compromised resources. For instance, the use of compromised domains, as opposed to domains set up by the spammers themselves, makes it harder for spam to be blocked based on the presence of a spam domain — at least harder for it to be blocked without a risk of false positives.
We saw a clear example of this in the latest test, when several dozen emails from the same campaign managed to bypass all but a few spam filters in the test.
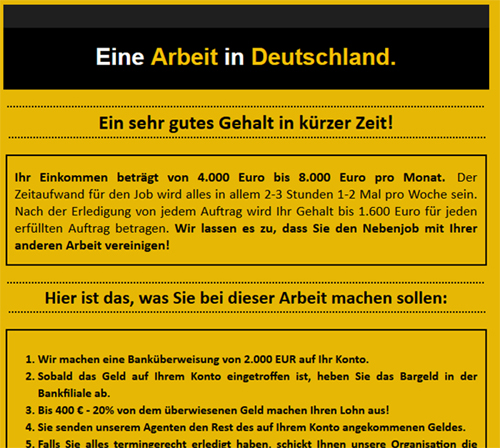
The campaign targets users in Germany and isn't too hard to spot as job recruitment spam. In fact, the promise of receiving a fair amount of money in return for very little work suggests that the spammers are looking for money mules.
What made these emails difficult to filter was that they were sent from Outlook.com accounts that were likely generated for the purpose. The high delivery rates means that the spammers would have needed to send significantly fewer emails for the campaign to be successful, thus turning spam from a quantitative problem into a qualitative one.
This month's VBSpam report can be viewed here in HTML format, or downloaded here as a PDF.
Posted on 28 April 2015 by Martijn Grooten