Posted by Virus Bulletin on May 1, 2015
Clean sweep of passes in VB100 test on Red Hat Enterprise Linux.
2015 will yet again not be the 'Year of the Linux Desktop', yet behind the scenes' Linux plays an important role in many organisations by running the servers on which files are stored centrally. Such servers could easily become centres of malware infection; hence a number of companies offer anti-malware solutions that aim to protect them.
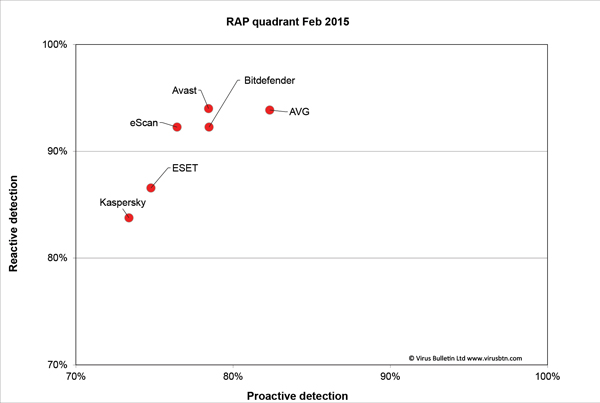
In VB's annual VB100 test on Linux, John Hawes and his team tested six of these solutions — Avast, AVG, Bitdefender, eScan, ESET and Kaspersky — all of which achieved a VB100 award.
As always, readers are encouraged to read the full test report, which contains full details on the products' detection rates, performance and stability. The report can be viewed here in HTML format, or downloaded here as a PDF (no registration required).
Posted on 01 May 2015 by Martijn Grooten