Posted by Virus Bulletin on Jun 19, 2015
Exploit kit currently being tested focuses primarily on Flash Player exploits.
Nuclear, Angler, Magnitude and Rig. Security researchers know we're talking about exploit kits (or browser exploit packs), toolkits that automate the exploitation of client-side vulnerabilities and thus facilitate infection through drive-by downloads.
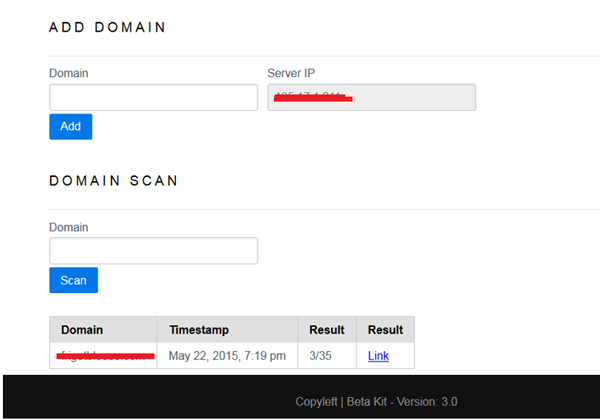
Today, we publish an article by researchers Aditya K. Sood and Rohit Bansal, in which they look at a new exploit kit, 'Beta'. Though it is still in a testing phase, Aditya and Rohit managed to gain access to one of its command-and-control servers and were thus able to learn details of the exploit kit, including its price, the structure of the URLs it uses, and the exploits that are being used.
In line with a trend seen in other exploit kits, Beta's main focus is on exploits in Adobe's Flash Player. It also checks domains and executables against detection by anti-virus engines.
Last week, security blogger 'Kafeine' wrote about a different version of the same exploit kit, which researchers have dubbed 'Sundown'.
By publishing details of this exploit kit, we and the paper's authors hope to raise awareness of its existence, which could help with swift detection as soon as it starts to be used more widely.
You can read the paper here in HTML format or here as a PDF. Remember that all content published by Virus Bulletin can be read free of charge, with no registration required.
Posted on 19 June 2015 by Martijn Grooten