Posted by Virus Bulletin on Jun 11, 2015
Option hides the servers, without having to include a Tor client in the malware.
The authors of the Vawtrak trojan (also known as Neverquest) have moved some of its C&C servers to Tor hidden services and made the malware use Tor2Web to connect to them, Fortinet researcher Raul Alvarez writes.
The use of hidden services for C&C servers isn't a new technique and is often used because it makes botnets less vulnerable to sinkholing and takedowns. Using Tor2Web meant that the Vawtrak authors didn't have to include a Tor client in their malware: it uses normal HTTP to connect to the Tor2Web server, which then uses Tor to connect to the actual hidden service.
This does leave the connection vulnerable to detection by IDS or IPS, but that's likely of little concern for the authors of the banking trojan, many of whose victims are ordinary home users. Of course, those using Tor hidden services to evade censorship or to engage in whistleblowing should never use services like Tor2Web.
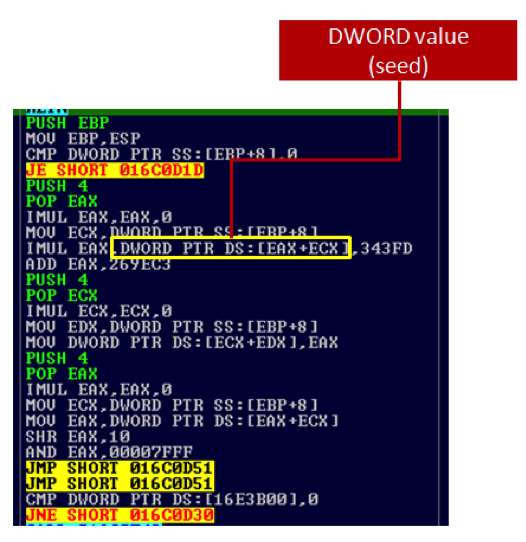
The new version of Vawtrak includes a domain generation algorithm (DGA) to generate the .onion domains of the C&C servers. However, as there is little choice in such domains (they are hashes generated based on the public key of the hidden service), the algorithm will be implemented to generate values already known to the authors; hence the DGA is likely used only to prevent detection of the C&C domains, not to generate domains that can subsequently be registered.
Earlier this year, VB published Raul's paper 'Nesting Doll', in which he analysed the various layers of obfuscation in Vawtrak itself.
Posted on 11 June 2015 by Martijn Grooten