Posted by Virus Bulletin on Jul 31, 2015
Support scammers not lying about a malware infection for a change.
During our work on the development of the VBWeb tests, which will be started soon, we came across an interesting case of an infected website that served not only the Nuclear exploit kit, but also a fake blue screen of death (BSOD) that attempted to trick the user into falling for a support scam.
When a (legitimate) website includes (legitimate) advertisements, these ads themselves are rarely included in the HTML code. Rather, the HTML contains some code — typically JavaScript — that loads content from an ad server, which shows the advertisements in the browser. This means a selection of advertisements can be shown that are deemed the most interesting to the particular user, while it also allows advertisers to bid for "eyeballs".
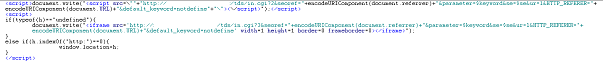
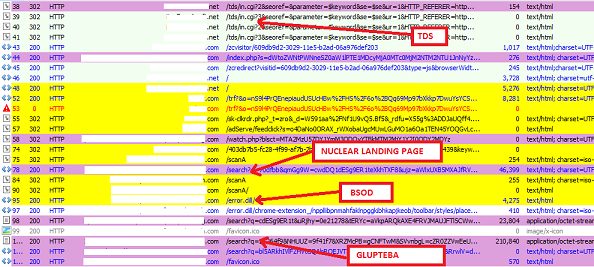
Malicious websites work in the same way. Indeed, the compromised website in question (which, unsurprisingly, ran a 2008 version of WordPress) contained a little bit of obfuscated JavaScript that inserted an iframe as well as loading another piece of JavaScript, both from the same server. These are two examples of traffic distribution systems (TDS), which are the malicious equivalent of the code used by ad networks to display relevant ads.
What was interesting was that when we opened the site in our test lab, we found that both URLs were opened by the browser. One of them served the Nuclear exploit kit, which used a Flash Player exploit to deliver the Glupteba downloader, which would likely have downloaded another piece of malware. Glupteba is commonly seen as the payload for Nuclear.
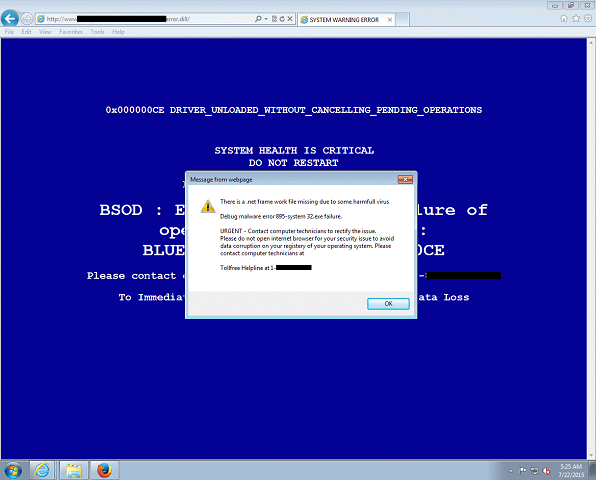
The other URL made the browser show a fake BSOD with a pop-up urging the user to call a toll-free US number, where a phone operator would likely trick them into paying a large sum of money for little to no protection. Earlier this month, a Malwarebytes researcher wrote about this particular trick, which despite its apparent simplicity contains some anti-analysis tricks.
It is unclear why both pages were served. It might be that the malware authors were just being greedy and trying to maximise their chances of success. It might also be a bug on their site. In any case, for once, support scammers wouldn't have been lying about there being malware present on the victim's machine.
In the VBWeb tests we will test the ability of gateway-based security solutions to block such threats on the network. We are currently running a trial and noted that this infection and social engineering attempt was blocked by several solutions, though not all of them. Those interested in participating in these tests are asked to contact [email protected].
This research was performed together with Adrian Luca. We'd like to thank Jerome Segura (who last year spoke on support scams at VB2014, and who is one of the leading experts on exploit kits) for his input.
Posted on 31 July 2015 by Martijn Grooten