Posted by Virus Bulletin on Aug 14, 2015
Malware authors upped their game following 2014 disruption of No-IP.
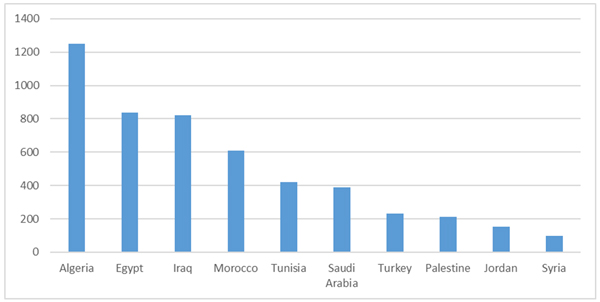
In June last year, somewhat controversially Microsoft moved against dynamic DNS provider No-IP and seized 22 of its domains, subdomains of which were used to spread and control the NJRat (also known as Bladabindi) and NJw0rm (also known as Jenxcus) malware families, both of which primarily operated in the Middle East.
A week later, Microsoft settled with No-IP parent company Vitalwerks, which regained control of the domains. This hasn't stopped its service from being used for the spread of malware though.
Today, we publish an article by Intel Security researchers Abhishek Bhuyan and Ankit Anubhav, who looked at current NJRat campaigns in the Middle East.
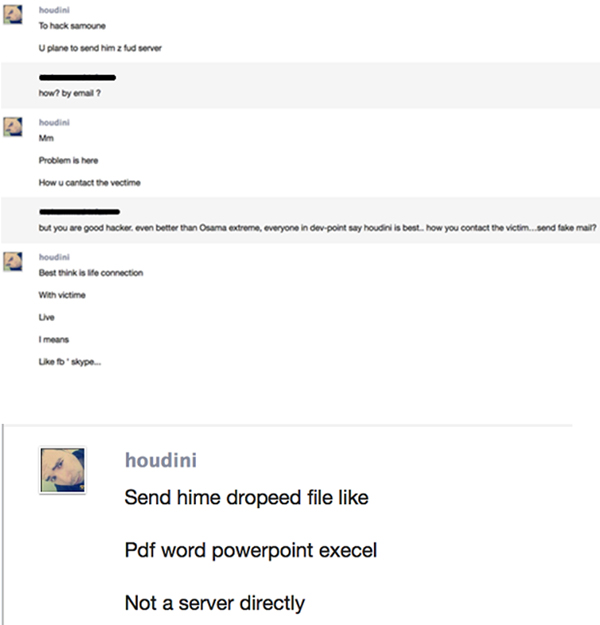
Historically, malware authors based in the region have made little effort to hide their goals, sometimes even calling their malware 'trojan.exe'. Recently, however, they have upped their game, one sign of which is an Arab cybercrime forum where tutorials are posted on how to make sure the malware isn't detected by different anti-virus vendors.
Abhishek and Ankit found more than 5,000 unique domains used, a little less than half of which were still active. Surprisingly, Windows XP remains a popular choice among those running NJRat, suggesting that their level of security isn't much better than those of their victims — many of whom, a Skype conversation with the malware author revealed, are sent the trojan executable disguised as a popular file type.
You can read the article here in HTML format or download it here as a PDF.