Posted by Virus Bulletin on Aug 11, 2015
Experts to cover various aspects of IoT (in)security in a range of talks.
As a reader of this blog, and hopefully as someone who will attend VB2015, you don't need to be told that more and more devices are being connected to the Internet, nor that this comes with some security issues. And while your fridge sending spam might not be that big a deal for you, your fridge or the Internet, things are different when it turns out that your car or your insulin pump can be controlled remotely.
Several VB2015 talks deal with the IoT, as it's most commonly called, and its security or (all too often) the lack thereof.
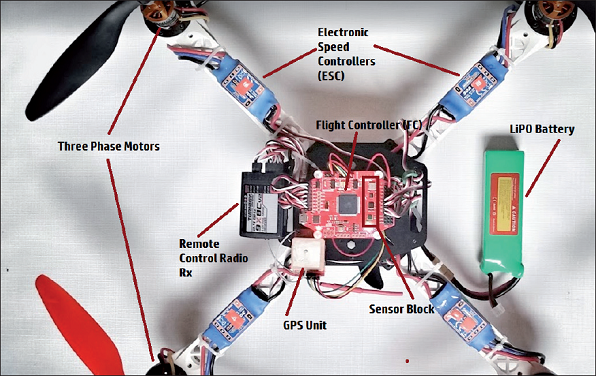
The ability to remotely control drones is, of course, an essential feature rather than a bug in these unmanned aerial vehicles (UAVs). At VB2015, HP researcher Oleg Petrovsky will present a paper in which he discusses various flight controllers for UAVs as well as the attack surfaces that exist: from malicious bootloaders and firmware to the ability to control the UAV by sending commands from a fake ground control station.
A paper by Microsoft's Jasmine Sesso and independent researcher Heather Goudey looks at the current state of malware targeting the IoT as well as what lies ahead for it — for example, in that magical year 2020 when, according to Gartner, the IoT will generate an extra $300bn in revenues. The paper also looks at current approaches to IoT security (including a number of Internet standards) and at recommendations made by the Federal Trade Commission (FTC). Finally, Jasmine and Heather look at the role anti-virus can play in these heavily restricted environments.
Two researchers from Avast, Martin Smarda and Pavel Sramek, have written a paper in which they discuss a module that has been added as a pilot to their product and which scans home networks for vulnerable devices. The idea behind the module is not just to inform users about insecure settings, default passwords and other kinds of weaknesses; in an era where security researchers are all too often ignored when they report vulnerabilities, their hope is that perhaps the crowd will be listened to.
In some cases, the risk to connected devices is far bigger than your smart TV being infected with ransomware: think of cars or medical devices. In one of this year's brand new Small Talks, Claus Cramon Houmann, a member of I am the Cavalry, will highlight the work this grassroots organisation does to make sure our devices become more secure and discuss with delegates how to gain optimal benefit from I am the Cavalry in Europe.
Have you been working on IoT security — or have you analysed a recent attack targeting connected devices? Why not submit a last-minute paper to fill one of the ten remaining slots on the VB2015 programme? You've got until 3 September to submit a proposal.
