Posted by Virus Bulletin on Sep 18, 2015
VB2015 presentation to include demonstration of technique against recent samples.
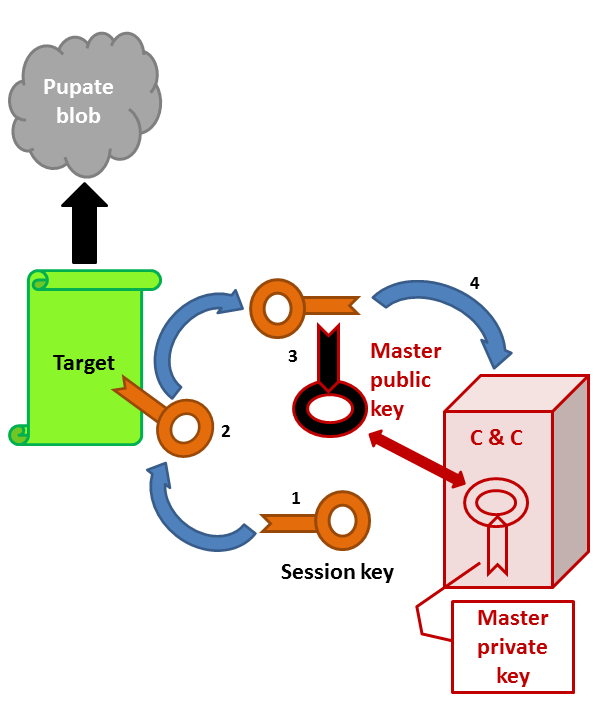
'The scary hack that's on the rise' is how Wired's Kim Zetter described ransomware in an overview article posted yesterday. Indeed, encrypting your files and demanding a ransom to decrypt them has become a very lucrative cybercriminal enterprise.
Of course, the best defence against ransomware is to make regular backups that are stored separately from the original device. But can security software perhaps play a role too and prevent ransomware from running in the first place?
Samir Mody and Gregory Panakkal, two researchers from K7 Computing in India, think it can. At VB2015 in Prague, they will present a paper 'Dead and buried in their crypts: defeating modern ransomware', in which they discuss a generic anti-ransomware solution they developed. Those who think anti-virus is all about signatures will be interested to know that the paper doesn't mention the word 'signatures' even once.
But presenting a nice theoretical solution is one thing, making sure it actually works is something else. Hence Samir and Gregory are asking those attending the conference to submit new ransomware samples, which they will test their solution against during their presentation.
There are more than 50 other talks on a diverse range of security-related topics on the VB2015 conference programme. Why not join us in Prague? Registration is still open.
Posted on 18 June 2015 by Martijn Grooten