Posted by Virus Bulletin on Nov 5, 2015
All participating full solutions earn VBSpam certification, while little delay is observed in spam filters.
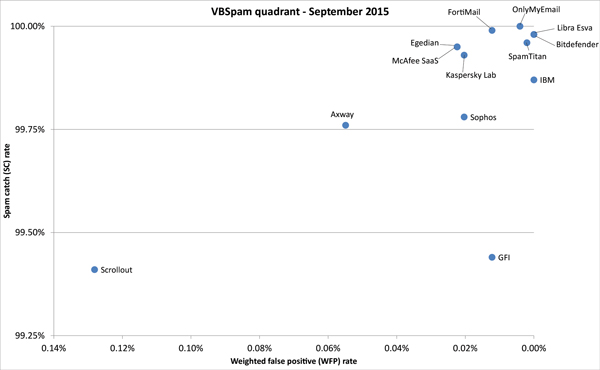
There is good news for those who rely on spam filters — which means everyone who uses email — as for the first time since July 2014, all participating full anti-spam solutions achieved a VBSpam award in VB's latest comparative spam filter tests.
Moreover, with an average spam catch rate of 99.84%, we can see that the spam problem continues to be very well mitigated.
Five solutions — Bitdefender, IBM, Libra Esva, OnlyMyEmail and SpamTitan — earned a VBSpam+ award for blocking more than 99.5% of spam, while blocking no legitimate emails and very few newsletters.
The VBSpam report can be downloaded here in HTML-format or here as a PDF.
Spam filtering happens almost entirely reactively: emails are blocked because they look like previously sent spam, because they are sent from IP addresses that have sent spam, because they contain links to known spam sites, or because they have other characteristics previously seen in spam. Often, rules for blocking spam are added automatically, based on end-user reports and detections by spam traps.
Therefore, a spam filter could artificially improve its performance by holding onto emails until rules have been updated, thus being able to catch more spam. As email is expected to work in real time, few people would want to use a mail server that adds significant delay to the delivery of emails.
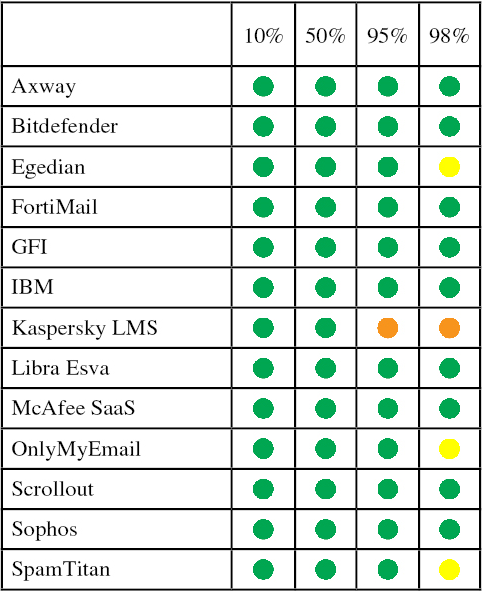
Although in our tests we have always made sure no product 'cheated' in this way, we have decided to start publishing the details of how long it takes each product to filter legitimate emails. For each product we ordered the legitimate emails by the time it took for them to be returned to us and showed whether the delay for the emails at the 10th, 50th, 95th and 98th percentiles was less than 30 seconds (green), less than 2 minutes (yellow), less than ten minutes (orange) or more than ten minutes (red).
As one can see, the table is mostly green, with only some small delays added by some products due to a small minority of issues. Although ideally all emails are returned immediately, we believe these small delays are not especially worrying as they may be caused by external factors.
Posted on 05 November 2015 by Martijn Grooten