Posted by Virus Bulletin on Nov 13, 2015
Aditya K. Sood and Rohit Bansal highlight a different side of an exploit kit.
Exploit kits are a serious plague on the Internet, made worse by the fact that the online advertisement ecosystem allows cybercriminals to run their malicious code on many websites. The kits are studied extensively by security researchers, who attempt to follow their development as the kits' authors try to make sure detection is evaded.
Today, we publish a paper by Aditya K. Sood (Elastica) and Rohit Bansal (SecNiche Security Labs), who look at another side of an exploit kit: the interface used by the malware authors who rely on exploit kits to get their malware installed on victims' machines.
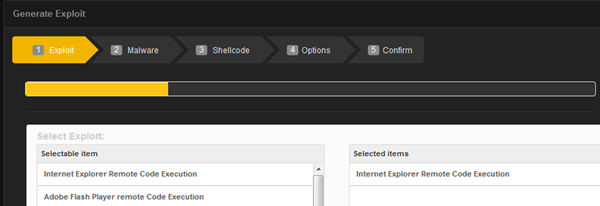
The kit they looked at is 3ROS, one of the lesser-known exploit kits. Its relative obscurity is not because 3ROS isn't user-friendly: the ease with which a malware author can fine-tune the kit to their needs should be an example for many a legitimate website. (The purpose of 3ROS, of course, should not.)
You can read the article here in HTML format or download it here as a PDF.
At time of writing, the domain on which 3ROS was being sold has ceased to resolve. However, that might not be the end of this particular kit. Security firm Proofpoint recently wrote about 'Hunter', a new exploit kit that is based on 3ROS.
Posted on 13 November 2015 by Martijn Grooten