Posted by Virus Bulletin on Dec 14, 2015
US presidential candidates regularly see their emails blocked by spam filters.
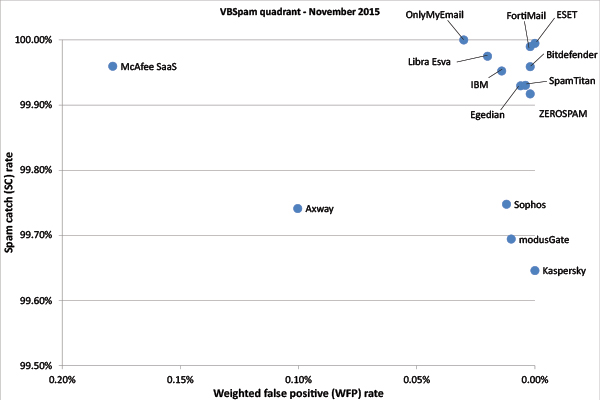
Yet again, there was good news for most participants in the bi-monthly VBSpam spam filters tests: spam catch rates for most products remained very high.
There was good news when it came to false positives too. Solutions blocked few to no emails from the corpus of regular legitimate emails, and few 'newsletters' too. This resulted in 14 VBSpam awards, with no fewer than eight products — Bitdefender, Egedian, ESET, FortiMail, Kaspersky, modusGate, SpamTitan and ZEROSPAM — earning a VBSpam+ award.
The VBSpam report can be downloaded here in HTML-format or here as a PDF.
This month, we also subscribed to newsletters from several US presidential candidates, giving us 23 emails from 10 different candidates in this month's newsletter corpus.
While 23 is a rather small corpus on which to base any firm conclusions, we found that these political emails were seven times more likely than other emails in the newsletter corpus to be blocked by participating spam filters. A small part of this may be explained by the fact that filters had not been trained on these particular emails — no doubt the fact that such emails are exempt from the US CAN-SPAM Act played a big part here too: there is no legal obstacle for US politicians and their staff who want to send unsolicited campaign emails, and many indeed do.
While the emails we received were all solicited, there was still a 10 per cent probability of a spam filter blocking them, which is high in a context in which many products are set to avoid false positives.
The single email from this group that was blocked the most was one from presidential candidate Marco Rubio, asking his alleged supporters to participate in a survey. Rick Santorum was the only politician whose emails (he sent two) weren't blocked by any full solution.