Posted by Virus Bulletin on Jan 5, 2016
BlackEnergy malware previously linked to targeted attacks in the country.
When in late December hundreds of thousands of homes in Western Ukraine suffered power outages, many people talked about the possibility of the interruption in power having been caused by a cyber-attack. But people always talk about cyber-attacks — the truth is almost always a lot more mundane.
However, this time things may have been different. ESET's Robert Lipovsky writes that several of the country's energy companies had been targeted by the BlackEnergy trojan around the time of the power cuts, something SCADA expert Robert M. Lee also wrote about, and which the Ukrainian CERT has confirmed to Forbes.
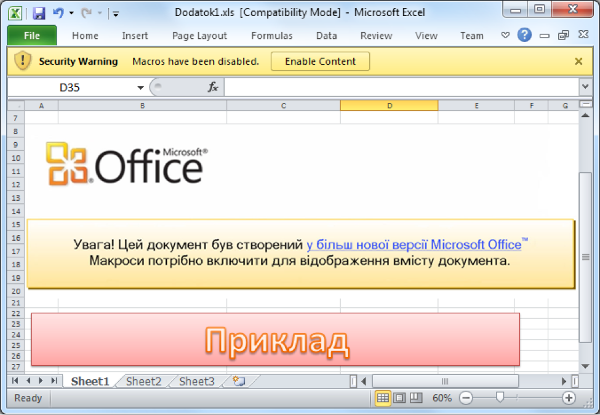
Robert Lipovsky explains how the trojan used the common methods of spear-phishing and malicious Office macros to infect its targets. After infection, BlackEnergy downloaded a second trojan, KillDisk, which appears to be designed to sabotage industrial systems, and which likely caused the outage.
Of course, it is worth keeping in mind that the power cut may have been an unintended side-effect of another sabotage operation. It is also worth noting that, given the highly polarized situation in Ukraine, any information that comes out of the country will have some kind of bias.
Still, this case shows that despite all the hype and fearmongering, actual cyber-attacks do happen from time to time and that Stuxnet wasn't a one-off incident. It also shows that such attacks don't need to be as advanced and sophisticated as Stuxnet was.
As for the BlackEnergy trojan, it isn't new and is not necessarily used by a single operator. At VB2014 in Seattle, Robert Lipovsky discussed how the trojan was used against various government targets in Ukraine.