Posted by Virus Bulletin on Jan 27, 2016
Simon Edwards discusses how to test the potentially untestable.
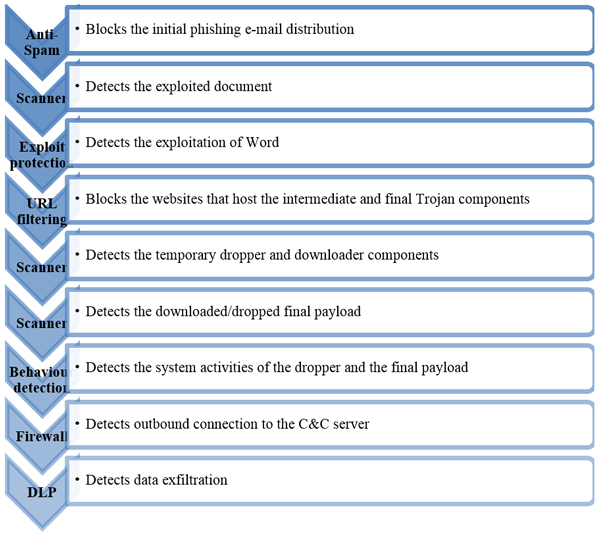
Like the term or loathe it, APTs have given rise to a new generation of security products that protect against these more targeted and sometimes more advanced threats. Often, such products come with bold claims about how they are able to fend off such threats in ways that traditional security products can't.
At VB2015, Simon Edwards (Dennis Technology Labs) presented a paper, written together with Richard Ford (Florida Institute of Technology) and Gabor Szappanos (Sophos), on how to effectively test such technologies.
You can read the paper, "Effectively testing APT defences", here in HTML-format, or download it here as a PDF, and find the video on our YouTube channel, or embedded below.
Are you interested in presenting your research at the upcoming Virus Bulletin conference (VB2016), in Denver 5-7 October 2016? The call for papers is now open.