Posted by Virus Bulletin on Feb 9, 2016
Kurt Baumgartner talks about Turla's extraplanetary activities.
Despite the hype around the subject, the tools used by most so-called APT groups are surprisingly mundane. But there are exceptions.
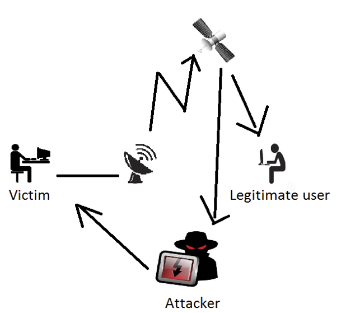
In September 2015, researchers at Kaspersky Lab published research on the Turla APT group (also known as Uroburos or Snake), which hijacked satellite Internet links for command and control communication. At the cost of a slow and unstable connection, it does a good job of hiding threat actors' real location.
A few weeks after this report was published, Kaspersky Lab researcher Kurt Baumgartner presented the VB2015 last-minute paper "TurlaSat: The Fault in our Stars" on this subject. We have now uploaded the video of Kurt's presentation to our website.
Are you interested in presenting your research at the upcoming Virus Bulletin conference (VB2016), in Denver 5-7 October 2016? The call for papers is now open.