Posted by Martijn Grooten on Feb 19, 2016
Virus Bulletin has been testing security products for more than 18 years, and in recent years, we have had many requests from product developers asking us to test their web security products. After all, whether malicious software is downloaded directly from websites or through sneaky drive-by downloads, the web remains an important infection vector.
In response to those requests we have built a new test suite to add to our existing VB100 and VBSpam tests.
The new test, called VBWeb, measures products' ability to block malware spreading through HTTP. The test's current focus is (corporate) gateway solutions that run on the network as an implicit or explicit proxy. We are looking to extend the test in the future to on-desktop and in-browser solutions.

Given how quickly web-based threats change, and given how many of them actively attempt to frustrate researchers (something we have also frequently run into), building a web security product is not a trivial task, and submitting such a product to a public test isn't something vendors do without serious consideration.
In this test, while there were several participants, the developers of Fortinet's FortiGuard appliance were alone in agreeing for their product to be tested publicly. Their confidence in the product proved to be well founded: it blocked all but a few out of hundreds of malicious downloads, as well as a significant number of live exploit-kits.
Indeed, with an 83% catch rate - well over the 70% threshold required for VBWeb certification - FortiGuard is a clear and deserved winner of the very first VBWeb award.
You can read the full report here in HTML format, or download it here as a PDF. The report describes the testing methodology in full detail.
From now on, VBWeb will be run every second month. Product developers who are interested in submitting a product for the test (publicly or privately) can contact Virus Bulletin's Editor Martijn Grooten at [email protected].
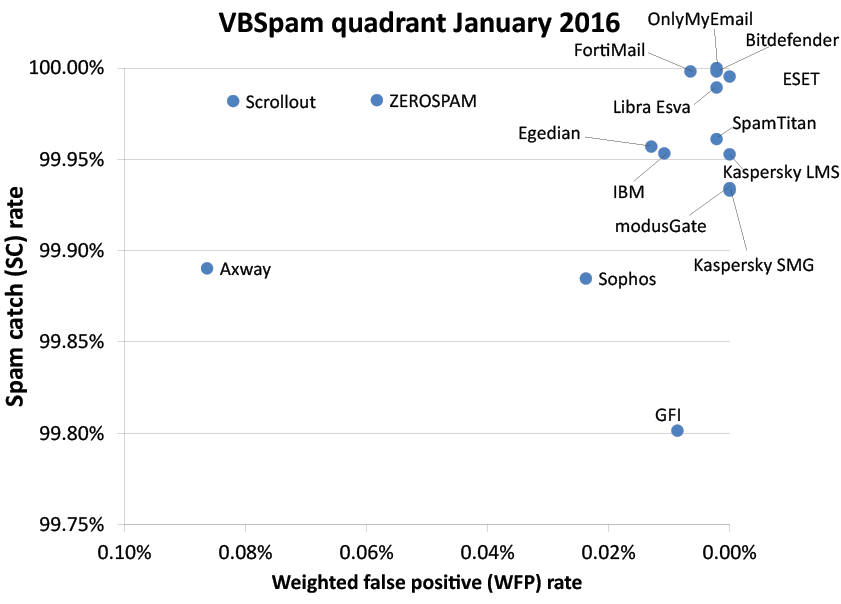
Of course, HTTP isn't the only infection vector systems administrators have to be worried about. But in the case of email, there is good news: all 16 participating full solutions achieved certification in the latest VBSpam test, which saw record catch rates. Ten products even achieved a VBSpam+ award, after blocking more than 99.5% of spam while also avoiding false positives.
You can read the full report here in HTML format, or download it here as a PDF.