Posted by Martijn Grooten on Apr 15, 2016
Malware infections are never fun, but ransomware is particularly nasty and the plague doesn't seem likely to cease any time soon: new families are spotted almost daily.
A small silver lining in this dark cloud is the fact that crypto is hard for the bad guys too: they have made many mistakes implementing their encryption algorithms, and this has helped security researchers write tools that recover files encrypted by quite a few malware families.
Of course, the release of such tools — and especially blog posts that explain in full detail how the tools work —gives the malware authors a heads up that they have made a mistake. At Botconf last year, Fox-IT researcher Yonathan Klijnsma, who maintains the Cryptowall Tracker, explained how the authors of Cryptowall hardened their encryption algorithm following public blog posts pointing out mistakes.
Moreover, for a not-so-tech-savvy victim, it isn't always easy to identify which ransomware is present on their system — a situation made worse by the fact that names and designs tend to be shared among multiple families.
Thankfully, there is now a solution for that. The people behind the MalwareHunterTeam have release the ID Ransomware tool, which allows anyone to upload a ransom note or an encrypted file and will then determine which of the more than 50 known ransomware families has encrypted the files.
Of course, there is no guarantee that there is a decryption tool available for the ransomware in question. The older families in particular tend to have crypto that can't be broken. But against this threat, every infected computer that we are able to decrypt is worth it.
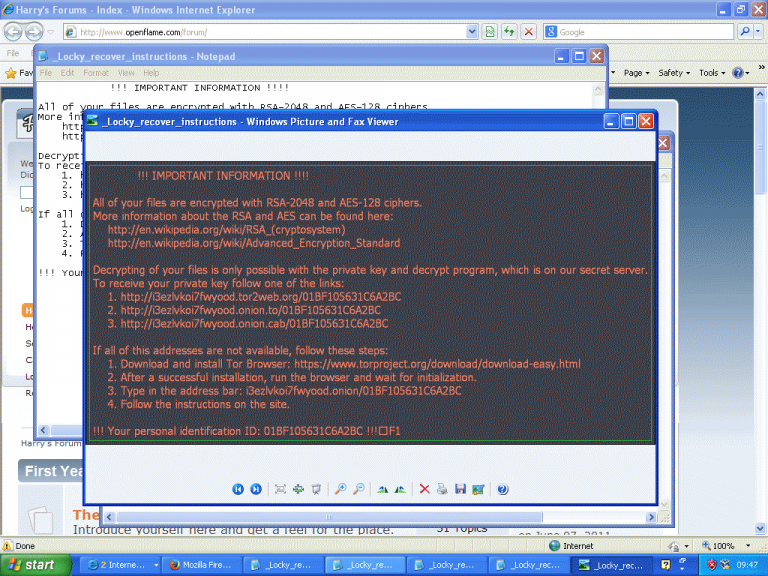 Ransom note of the Locky ransomware. Found in March during our VBWeb research.
Ransom note of the Locky ransomware. Found in March during our VBWeb research.