Posted by Martijn Grooten on Apr 26, 2016
I'm not usually one to spread panic about security issues, but in the case of the current ransomware plague, I believe that at the very least a sense of great concern is justified. And the threat is unlikely to disappear any time soon.
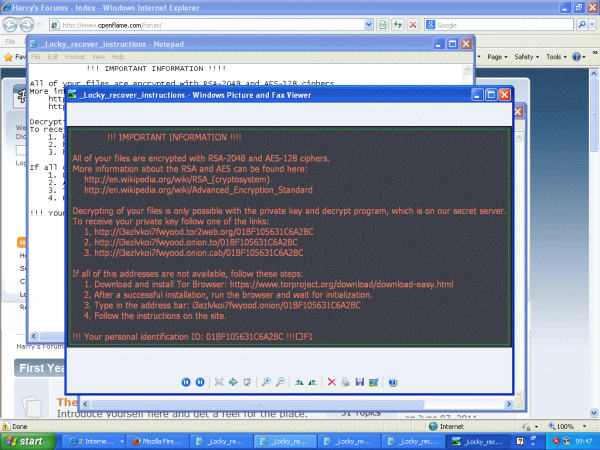
While there are certainly many things we can do to significantly reduce the risk of us getting infected — from applying all necessary patches and keeping offline backups, to running software that alerts us when files are suddenly being modified en masse — ultimately, ransomware does what we all should be doing: encrypting our files. The subtle but essential difference is that it does so with a key we don't have.
One reason why ransomware is so successful is that the ransom demanded is usually only a few hundred dollars — affordable to most people (ransomware tends to target users in Western countries) and often cheaper than the (perceived) value of the data that would otherwise be lost. However, security experts regularly tell affected individuals and organizations never to pay the ransom.
I think this is unhelpful advice.
For sure, paying the ransom should always be the last resort. We should help victims, and the jack-of-all-trades sysadmins who are likely going to assist them, find other ways to recover the data. Maybe backups have been kept. Maybe this particular ransomware is one for which a decryption tool is available. And maybe losing the data — which could also have happened because of a physical failure of the hard drive — is an expensive but valuable lesson on the importance of keeping backups.
But sometimes, none of this helps and the only sensible business decision left is to pay the criminals, much as it is bad and much as there is never a 100% guarantee that this will work. Crooks will be crooks, after all.
Of course, if everyone followed the advice never to pay a ransom, ransomware authors would come to find that it wasn't worth their effort, and the threat would eventually disappear. But this wouldn't happen instantly, and it really would depend on almost everyone not paying the ransom.
And if security experts suddenly had the power to make everyone follow their advice, maybe we should just tell people to patch instead.